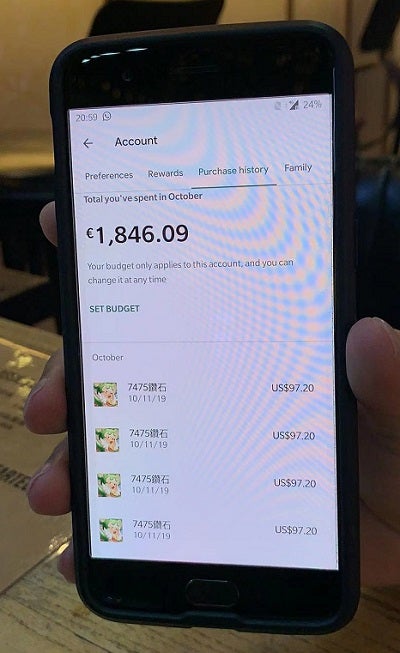
Wednesday night, a traveler boarded a plane in Kuala Lumpur and flew into Shenzhen, China. Upon arrival, they connected to the Free Airport Wi-Fi to communicate with a waiting friend and received a text message about a purchase through the Google Play Store for €88.02. However, they hadn't made any purchase. They had simply connected to the Wi-Fi and sent a text message saying they had landed. They watched helplessly as multiple purchases for the same application drained their accounts.
The next night, over beers, we looked over the “purchases,” offered suggestions on how to get the money returned, and discussed where to exchange currency.
We’d like to say there was no way he could have avoided this tragedy – but there was. The friend of our unlucky traveler mentioned a recent Wi-Fi Safety educational video I had forwarded her, produced by my company, Sangfor Technologies, in which we explain the risks of using unknown Wi-Fi. Welcome to the Zero Trust World of Free Wi-Fi.
It simply isn’t safe to connect to any untrusted Wi-Fi anymore. Rogue Wi-Fi can be set up with the most basic tools – with enticing words like “Free” or “Fast” attracting anyone who happens to be passing in need of a quick connection. These rogue Wi-Fi networks host several insidious attacks.
A Man-in-the-middle attack positions the threat actor between the Wi-Fi user and anyone they connect with, intercepting all communications, culling information and eavesdropping on everything you do.
Malware is commonly known. Once your mobile device is infected, this infection can spread to any connected device or on any other network, endangering all those you come in contact with.
Snooping & Sniffing allows hackers using special software to watch everything you do online, enabling them to catch log-in credentials or potentially hijack your accounts.
Ad Hoc attacks use a peer-to-peer network to connect two computers directly. Thus, a hacker can be directly connected to your computer – seeing what you see and potentially, everything you don’t.
Worm attacks have slightly different functions than viruses, as viruses attack specific programs and are somewhat limited in their function. Worms are free to attack any program they encounter and can move from device to device on a network.
These unsecured Wi-Fi networks, or public networks without password requirements, are found in coffee shops, shopping malls, airports and train stations – basically anywhere with lots of foot traffic and mobile devices. While this single traveler’s story might not move anyone to action, he was certainly not the only traveler to connect to that unsecured network on Wednesday evening, and each traveler will go away from the airport telling friends, family, coworkers, credit card fraud departments and banks exactly where they were when the theft occurred. We have a personal responsibility to protect our devices and be smart about connecting to public Wi-Fi, but businesses are also responsible for keeping their customers safe.
- 1. Place your router in a physically secure area
- Change the default log-in information on the router and strengthen the password
- Set a readily identifiable network name
- Keep software updated
- Use multiple firewalls or next generation firewalls (NGAF)
- Configure for both public and private access
- Access point scan for rogue APs
- Contact Sangfor Technologies for help keeping your network secure
Why Sangfor?
Implementing a Next-Generation Security solution like Sangfor NGAF & Endpoint Secure means utilizing the power of AI for all-around network protection. Sangfor has researched, designed and developed NGAF & Endpoint Secure, an end-to-end comprehensive Enterprise Protection solution, to be an easy-to-use converged security solution designed to protect users from internal, external, existing and future threats and is proactively updated regularly to keep your network safe from those with malicious intent. It’s already in use throughout the APAC region and Europe by government bodies, retail stores, universities and financial institutions, as you can see HERE.
The reputation of a business can be easily damaged, and the theft of thousands of Euro will certainly remain in the minds of this traveller and all those he comes in contact with for as long as he can tell stories over pints. Protect your customers and patrons and secure your networks, before you become the next hacking horror story.
Founded in 2000 and a publicly traded company as of 2018 (SANGFOR STOCK CODE: 300454 (CH)), Sangfor Technologies is the global leading vendor of IT infrastructure solutions specializing in Network Security and Cloud Computing. Visit us at www.sangfor.com to learn more about your NGAF options, benefits and functions, and make your IT simpler, more secure and more valuable.





