
Black Hat USA 2021, mecca of the most cutting-edge security researchers in the world, kicks off on July 31 featuring two Sangfor studies, which will be presented to the world's security technology experts and tens of thousands of security researchers from around the world.
Black Hat was founded in 1997, and is recognized as the world's top gathering in the information security industry, and the most advanced technical information security conference. Today, Black Hat holds one yearly conference in the United States, Europe and Asia, with Black Hat USA the largest and most authoritative organization and the best window for understanding future security trends. Security technology researchers are taking the stage at Black Hat USA to share their findings with the world, a high honor in security circles. It is known that among the thousands of topics submitted by security technology researchers around the world, very few make the final list of presenters. This year, two Sangfor studies are being recognized; “Delve into Spooler services: Discover local rights and remote code execution vulnerabilities in Windows printer services” and “Attack Windows COM/WinRT Service" led by security researchers Zhiniang Peng, Xuefeng Li and Bin Li.
Multiple 0-Day Vulnerabilities Were Found in Spooler
Avoiding a Repetition of Disaster
Ten years ago, the Stuxnet worm used a Windows Printer Spooler privilege upgrade vulnerability to destroy Iran's nuclear enrichment centrifuges and infect more than 45,000 networks, directly crippling equipment at Iran's nuclear facilities and at critical institutions around the world. Over the past decade, the potential security risks of the Spooler service have only increased, with numerous program bugs discovered, that could lead to disaster.
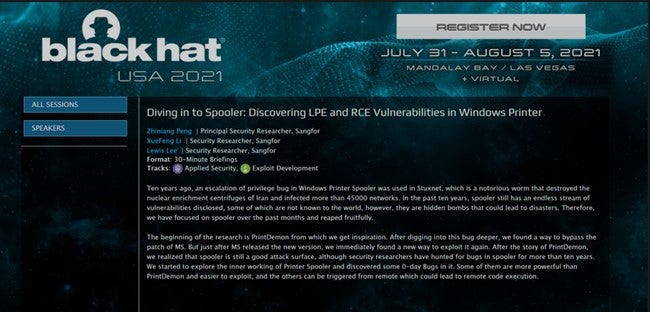
An overview of the topic of "Delve into Spooler Services: Discovering Local Authorization and Remote Code Execution Vulnerabilities in Windows Printer Services" (image from Black Hat website)
Although security researchers in the industry have been looking for bugs in Spooler for more than a decade, this year, security researchers at Sangfor discovered multiple 0-day vulnerabilities in Spooler, and will present their latest research findings in their presentation “Delve into Spooler services: Discover local rights and remote code execution vulnerabilities in Windows printer services” at the Black Hat USA 2021 conference.
Sangfor Discovers Hundred Windows COM/WinRT Vulnerabilities
Nip threat in the bud
Windows COM/WinRT components are widely used in Windows systems, a common component of Windows UWP applications, and is widely used for cross-process communication. If there are security vulnerabilities in these components, a vast majority of Windows systems may be exposed. The attacker can take over the victim host completely, using these security loopholes, and carry out malicious operations like mining, blackmail and sensitive information collection.

"Attack Windows COM/WinRT Service" topic overview (picture from the official website of Black Hat)
In the past year, security researchers Zhiniang Peng and Xuefeng Li have discovered more than 100 vulnerabilities in Windows COM/WinRT services, and will share their tips on exploiting these vulnerabilities at Black Hat USA 2021.
Sangfor has been focusing on the research of network security attack and defense technology, using the perspective of the attacker to solve network security issues. In the future, Sangfor will continue to improve professional technical attainments, in-depth insight into network security threats, continue to enable users to provide the best in network security.





