TSMC Supplier Suffers Data Breach
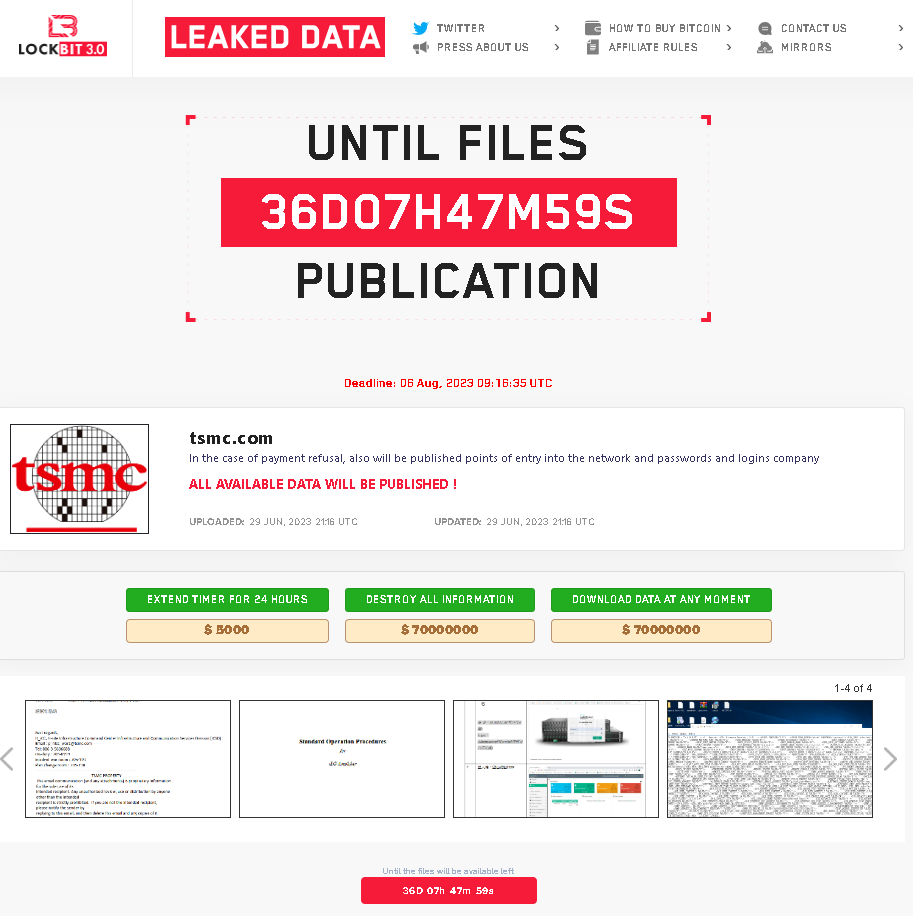
On June 29, 2023, Sangfor FarSight Labs discovered that the LockBit ransomware group listed TSMC (Taiwan Semiconductor Manufacturing Company) on the LockBit 3.0 website.
The appearance of TSMC on the website immediately drew significant media attention, owing to its status as the world's largest chipmaker with an annual revenue of nearly $75 billion USD in 2022. The attackers made a staggering ransom demand of $70 million USD, tying for the third highest ransom ever recorded by a ransomware group. Here are the four highest ransom demands in history:
| Ransomware Family | Victim | Ransom Demand |
|---|---|---|
| Hive | MediaMarkt | $240 million USD |
| REvil | Acer | $100 million USD |
| REvil | Kaseya | $70 million USD |
| Lockbit3.0 | TSMC | $70 million USD |
This is the second major ransomware attack TSMC has suffered in recent years, with the company falling victim to a devastating WannaCry ransomware attack that forced it to shut down production in August 2018.
About the LockBit Ransomware Family
LockBit is the notorious ransomware family from a Russian-speaking threat group that emerged in September 2019. Originally dubbed “abcd” ransomware, this family has undergone several iterations, culminating in the development of LockBit 3.0, which was responsible for the attack on TSMC. Also known as LockBit Black, this latest strain incorporates code elements from the BlackMatter and DarkSide ransomware families. It introduced anti-analysis & evasion techniques, password-less execution, and built-in command-line parameters, among other features to enhance its evasiveness and maximize its impact on targeted systems.
Impact of the TSMC Cyber-Attack
According to TSMC, the party impacted by the breach is identified as one of its suppliers, Kinmax Technology. In response to the incident, TSMC promptly initiated its security response protocols and standard operating procedures, resulting in the immediate termination of data exchange with the supplier. However, LockBit claims to have acquired TSMC's passwords, login credentials, and network entry points from Kinmax Technology and threatens to disclose this sensitive information if TSMC fails to make the payment.
Kinmax Technology has publicly acknowledged the discovery of an attack on an internal specific testing environment on June 29. The affected area was an engineering testing section, which serves as a system installation environment for customers. The company has confirmed the unauthorized access and theft of data, including installation configuration files. However, Kinmax Technology assures that this data is unrelated to the application used by their customers, emphasizing that no customers have been compromised as a result. Kinmax Technology specializes in providing IT services such as networking, cloud computing, storage, and database management to its clients. While Kinmax collaborates with various partners including Microsoft, Cisco, and VMware, it remains unclear at present whether these organizations have also been impacted by the breach.
LockBit shared several screenshots of the stolen data on its site, including information related to TSMC.
Sangfor Solutions
The following Sangfor products and services provide protection against the LockBit 3.0 ransomware family:
- Sangfor NGAF (Next-Generation Firewall)
- Sangfor Endpoint Secure (Endpoint Detection & Response)
- Sangfor Cyber Command (Network Detection & Response)
- Sangfor Cyber Guardian (Managed Detection & Response Service)
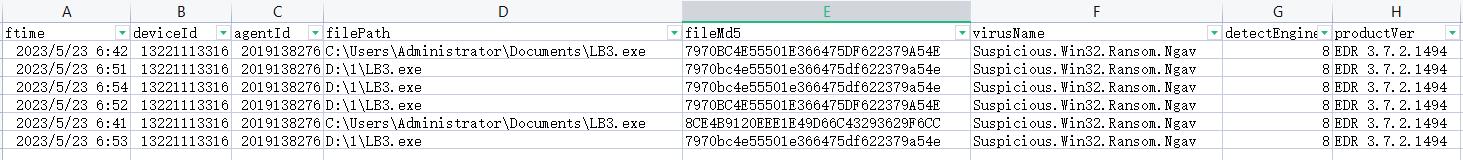
Sample of LockBit attacks blocked by Sangfor Endpoint Secure
About Sangfor FarSight Labs
Sangfor FarSight Labs researches the latest cyberthreats and unknown zero-day vulnerabilities, alerting customers to potential dangers to their organizations, and providing real-time solutions with actionable intelligence. Sangfor FarSight Labs works with other security vendors and the security community at large to identify and verify global cyberthreats, providing fast and easy protection for customers.





