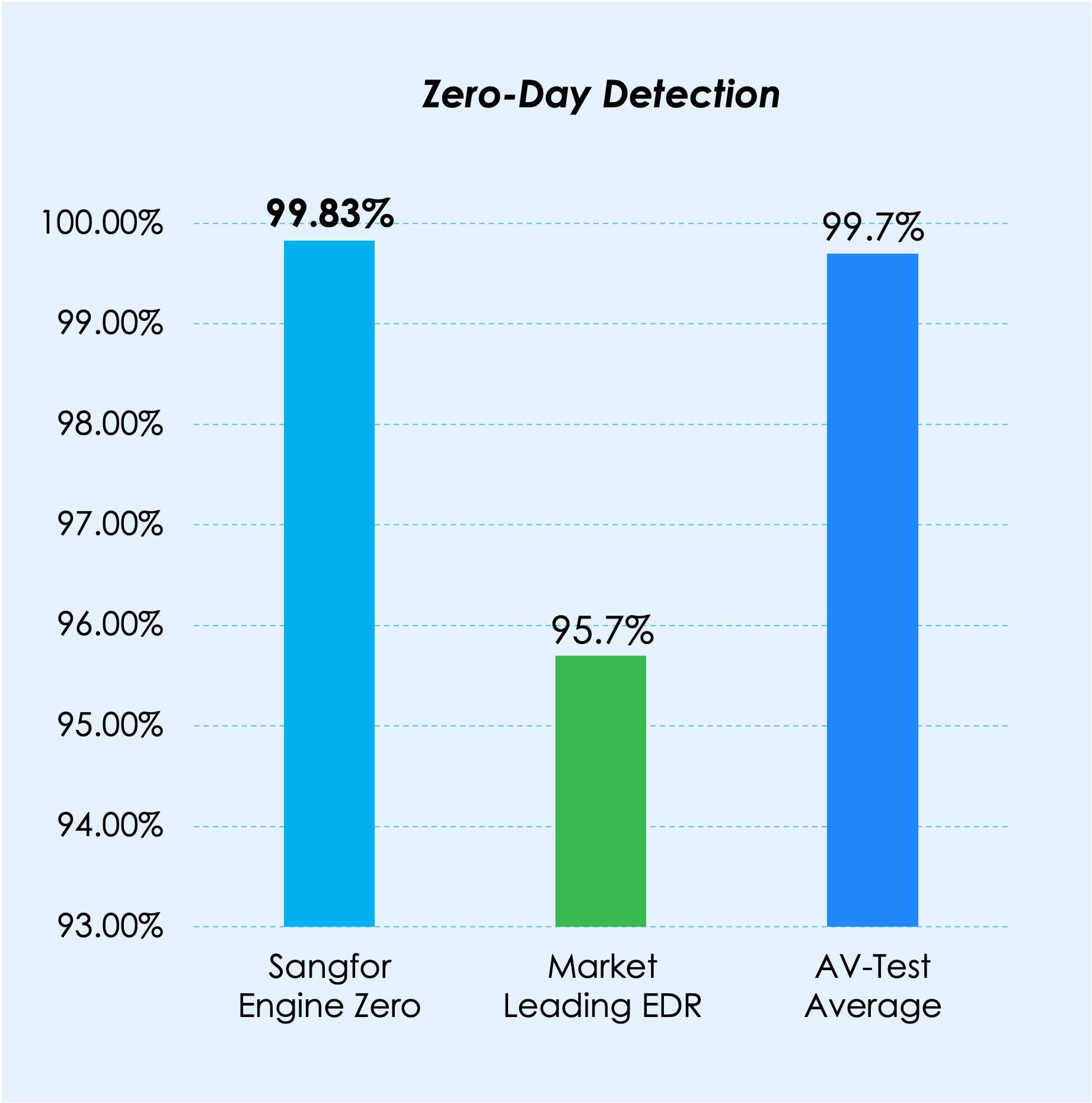
Athena NGFW integrates with Sangfor Engine Zero, an AI-powered malware detection engine. Engine Zero was developed using advanced machine learning models and AI algorithms, enabling Athena NGFW to achieve a 99.76% detection rate for both known and unknown malware across the internet.