What is Incident Response?
Incident Response is an organized process or phase of methodology that an organization uses to respond and deal with a security incident or data breach. Any data breach could have potentially significant impact on both sensitive customer data and on company confidential intellectual property, time and resources. In order to ensure damages are reduced, incident response is needed for an organization to deal with any security incidents and recover after different types of malware attacks.

Imagine the incident response process as to how a firefighter reacts and responds in the event of a fire.
We've discussed types of malware and several common transmission methods for malware to infect or spread within an internal organizational network in Part 1 of this series. It is important to know about the attack vectors that malware could use to propagate in the network. To combat this issue, you must prepare an Incident Response plan to outline security strategies or risk mitigation plans, to reduce these malware attack vectors and risk exposure. Implementation of firewall, secure email gateway, spam filtering, vulnerability management, and many other security control strategies could make the difference between survival and disaster.

Is Incident Response Needed by Organizations?
A recent study conducted by the Ponemon Institute on behalf of IBM, found that a vast majority of organizations surveyed are still unprepared to properly respond to cybersecurity incidents, with 77% of respondents indicating they do not have a cybersecurity incident response plan applied consistently across the enterprise.
Why is Incident Handling Important?
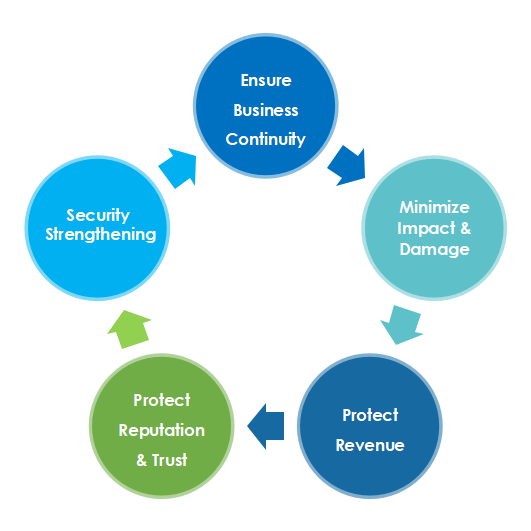
The top priority for an organization in handling security incidents is to ensure business continuity, minimize the impact of ransomware attacks, and continue to serve customers and users. By following a proper incident handling process and preparing a proper incident response plan, we can make the investigation process smoother, more efficient, and more effective. With quicker corrective and recovery action, we can ensure that business can be recovered in a shorter time.
What Will Happen if you Don't Handle Incident Response Correctly?
With proper incident response handling, knowledge, and skillsets, we can minimize the impact and damage done by malware or ransomware and protect revenue, reputation, and trust. Imagine your company is attacked often – or even once. What will your shareholders think if you don’t repair the issue and take proper precautions? In addition, if companies allow advanced ransomware to attack, collect and exfiltrate confidential company data and customers’ Personal Identifiable Information (PII), customers and shareholders will gradually lose trust in the organization and leave. Eventually, revenue, company share price, reputation and trust will drop. Finally, without proper incident handling, you wouldn’t know how and when an attacker gained entry, how to fix the issue or how to improve the overall security posture.
Contact Us for Business Inquiry
Incident Response Plan
There are four main steps in Incident Response Planning
- 1. Preparation
- 2. Detection and Analysis
- 3. Containment, Eradication and Recovery
- 4. Post-Incident Activity
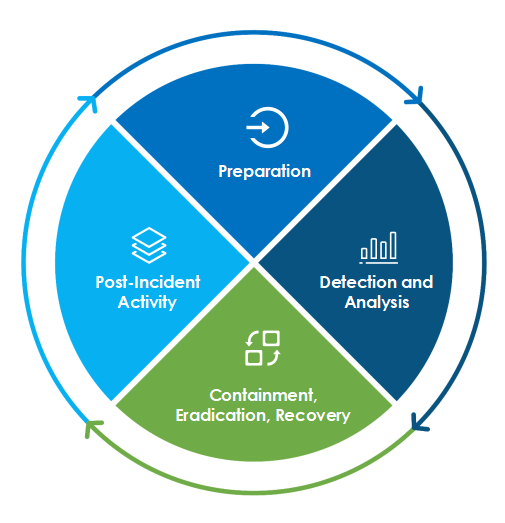
1. Preparation
First step, Preparation. When beginning the process of securing your network, first we prepare for attacks which take place daily, hourly, or even minute-by-minute, using automated tools. You never know when a malicious script or bot gains access to the company data – unless you are prepared for an attack. Not only do you need to plan your strategy properly, but you should have immediate access to basic information, including contact info for a Cyber Incident Response Team (CIRT). This information is useful to accelerate the communication process and make the response more efficient. One of the important components to prepare is backup and a Disaster Recovery (DR) server. It is important to have a DR server that can continue to serve business operations while investigating and recovering the production server. Daily backup is also required to keep a copy of the latest business data within easy reach.

2. Detection and Analysis
Proper Detection and Analysis is required for organizations to be prepared to respond to any incident, but should focus on preparing for incidents that use common attack vectors. Different types of incidents use different types of attack vectors and require different response strategies. An organization should always be aware of potential attack vectors and externally facing attack surfaces. Next, look for signs or symptoms of the attack, like sudden increases in attack count from specific IP addresses, slow network traffic or bandwidth performance, or pop-ups. Once you’ve discovered an anomalous or abnormal sign, look for indicators like security logs from network security devices, audit logs, web server logs, real-time network sniffing, and event viewers, to assist in further investigation.
Once you are equipped with the right data, you can perform further analysis of the security incident. Incident detection and analysis would be easy if every precursor or indicator were guaranteed to be accurate, but unfortunately, this is not always the case. False positives from security products and insecure daily practices like human mistakes or misconfigurations, will affect the analysis process. In this case, more time is required for the IT security team or system administrators to analyze and investigate the problem. We should always maintain industry best practices to maximize the accuracy of indicators, as well as the availability of all logs.

3. Containment, Eradication and Recovery:
In this phase of the incident response plan, once a security event is verified, you must analyze symptoms and plan a strategy for recovery and correction.
- First is Contamination: gather evidence including audit logs, email messages or malicious executable files. This evidence, together with the time, date, and location, are required to properly analyze and investigate the chain of events. We need to uncover the kill chain, including how the attack entered the environment, from which attack vector or surface it came, which vulnerability was exploited and if the malware has spread to other systems. If the organizations do not know where their risks and vulnerabilities are and take no action, these risks, threats, and vulnerabilities will remain there forever and will be exploited by attackers again.
- Next, we Eradicate the components of the incident, install antivirus software to kill off the malware, disable breached user accounts and remove the webshell.
- Finally, you Recover and restore systems to a healthy state and confirm that the systems are functioning normally.

4. Post Incident Activity
The last step in the incident handling process is Post-Incident Activity. This is one of the most important parts of the incident response process but is frequently neglected by organizations. From most organization’s perspective, after an attack and encryption, when the IT administrator has discovered the incident, reformatted the servers and brought them back online and recovered business operations, that’s in – case closed. This is not sufficient for future protection. Holding a post-event meeting to discuss the impact is a good start toward future incident handling. This meeting provides a chance to review the incident, intervention methods and results. Following points needs to be discussed in the post-event incident response meeting:
- 1. Did the IT team and management perform the right steps during the incident?
- 2. Was there proper and timely communication?
- 3. Were there any steps that weren’t taken that could potentially speed up the recovery process?
- 4. What corrective actions could be taken to further improve the investigation, analysis, and recovery process?
This process can help an organization to improve efficiency and effectiveness in handling future incidents. Apart from preparing an incident report that summarizes the incident details, the steps taken, and the discoveries during incident response process that need to be reviewed by higher management or compliance regulatory, the organization should work on strengthening the security controls.
Security control strengthening is not a one-off process. Powerful cyber threats, advanced attack techniques, mutated malware, zero-day vulnerabilities and advanced persistent threats (APT) can be difficult to eliminate with only one assessment. Properly deployed and updated security controls, safeguards and countermeasures mitigate risks to confidentiality, integrity, or availability in a system. The controls may impact or modify the behavior of people, processes, or technology, and may include physical, management, operational and process control. These security controls should be reviewed and revised often, preferably every quarter, for a fast-changing environment, and every six months for a steady environment with no new system or new configurations.
In a nutshell, implementing a proper incident response plan is a way to secure your IT infrastructure which not only helps you handle ransomware correctly, but also prepares you to fight for future cyber-attacks Contact Us for further inquiries.
Sangfor Incident Response & Compromise Assessment Services
In the event of an attack, Sangfor Incident Response (IR) starts with an investigative service which inevitably locates and contains the malware. Sangfor experts then classify the malware or ransomware family and trace the origin to stop the attack. Then they provide recommendations to improve security and on strengthening network defense to reduce security risk in the future.
Sangfor provides a network threat identification, analysis, and risk assessment (Compromise Assessment) service to customers who have suffered malware attacks and fear more unknown threats bypassing their existing security protection mechanisms. This service uncovers any hidden malware or backdoor events, data leakage, exploitation, brute force attacks, reconnaissance, east-west attacks and any anomalous UEBA (User and Event Behavioral Analytics) events.
Why Sangfor?
Sangfor Technologies is an APAC-based, global leading vendor of IT infrastructure solutions specializing in Network Security and Cloud Computing. Visit us at www.sangfor.com to learn more about Sangfor’s Security solutions, and let Sangfor make your IT simpler, more secure and valuable.





