Sangfor Next-Generation WAF
Background
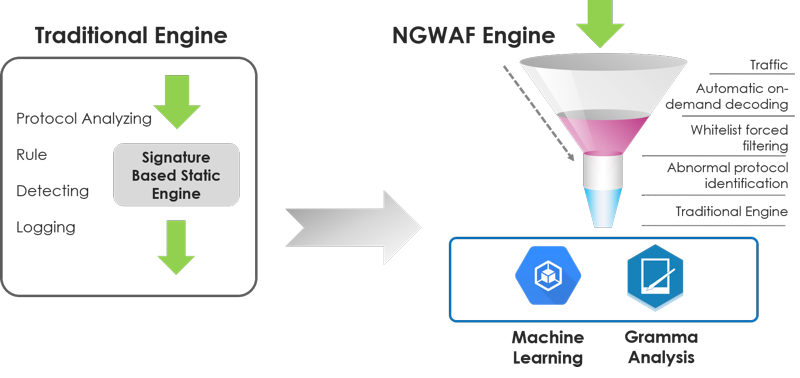
The Next Generation WAF engine, integrated with Sangfor's NGAF, was developed to protect against advanced web-based attacks like SQL injection, web shells, struts2 injection and deserialization flaws. Sangfor's Application Layer Firewall uses machine and deep learning to analyse attack behaviours, enhancing detection rates and decreasing false positives common with traditional SNORT-based detection engines. By modelling attack behaviour, a threat model is created to easily manage applications' system threats.
The Next-Generation WAF Should Evolve In A More Intelligent Direction
WAF products are an increasingly powerful tool against application-layer attacks and are still the standard for many companies dealing with complicated and changing application-layer attacks. As the means of attack increase, corporate applications are becoming more and more complex, resulting in traditional WAF finding it harder to provide corporate applications with comprehensive protection. Many companies are disappointed with the accuracy and ability of WAF threat identification and defence supplied by other Web Application Firewall Vendors. Analysis of the working principles of existing WAF products makes it easy to determine that the root cause of this unsatisfactory result is the inefficiency of rule detection engines and regular expression matching methods adopted by traditional WAF products. Processing performance and methods of attack detection and interception are inadequate when facing complicated and varied Web application attacks.
Sangfor NGAF - Next-Generation WAF Defense Engine
1. Improve overall device processing efficiency with deep learning capabilities
Introduction of machine learning makes collection of the characteristics of blank traffic in the traffic layer easier and makes legitimate traffic flow faster with significantly improved device performance.
SANGFOR's next-generation firewall adopts blank traffic filtering on WAF engines, executes deep learning based on application-layer interactive content, establishes a deep traffic learning model and implements monitoring, learning and comparison for each web element. The whole process is complemented by the self-learning capability of devices without manual intervention, making self-adaptive adjustments according to web traffic change and forming blank traffic filtering capability. If there is traffic that obviously deviates from a normal traffic pattern, import it to the follow-up security detection process to ensure that legitimate traffic may continue to flow fast. It greatly improves the processing efficiency compared to traditional WAF architecture which unpacks for inspection in sequence.
2. Integrate business parse with recovery capability through business intelligence fusion engine
SANGFOR NGAF intelligently matches the business environment with a business intelligence fusion engine, matching parsing and recovery capability based on business dynamic characteristics. It has the capability to accommodate diverse businesses on the backend, including reverting business-specific content fast, executing security detection and providing comprehensive solutions for various attacks.
3. Accurately identify Web threat with deep threat detection engine
The SANGFOR NGAF threat detection engine integrates a lexical algorithm with syntactic algorithm and fully adopts artificial intelligence to implement depth analysis for threats. It provides a comprehensive solution for complex business environments, business data and development approaches in a real environment and locates and processes any abnormality immediately.
Behaviour-based data models may be established after acquiring AI learning experience data. Predict targeted events with these data models, giving core security capabilities the characteristics of self-learning, model self-development and business self-adaption.
SANGFOR NGAF, based on the security concept of proactive and effective protection, adopts the next-generation WAF defence engine to provide business with effective defence capability in comparison with the traditional WAF defense methods.