Prank phone calls have existed since communications began, where individuals use phone numbers with the intent of tricking or playing a joke with the person who answers at the other end of the line. But in more recent years, coupled with the adoption of the internet and technology, prank phone calls have grown into a much more dangerous and serious form of harassment, most notably known as swatting.

Now, there is a growing surge of swatting attacks in the world. But the particular problem is especially worrying in the United States, where the trend originates.
Although swatting has historically been carried out on gaming victims, it is now spreading to attack other high-profile individuals, such as celebrities and politicians. But according to new trends, swatting incidents are now reaching Fortune 500 companies, targeting employees, C-suite executives and board members. Therefore, organizations today need to prepare and remain vigilant in case of a swatting incident. In this article, we cover everything you need to know about swatting, including what swatting is, how to protect from one and what to do if your organization is a victim.
What is swatting? - Definition
Swatting (also known as "SWATing") is a term that derives from the United States’ specialized police forces, known colloquially as Specials Weapons and Tactics (SWAT) teams. According to the FBI, swatting has been around since the early 2000s but has been growing exponentially since then.
Swatting is when someone makes a hoax phone call to report a serious crime to emergency services. People carry out swatting attacks in an effort to then fool emergency services into sending a SWAT team to respond to the supposed emergency’s address. These false emergencies can cover several major events, like bomb threats, kidnappings, hostage situations and murder, to encourage the most serious response levels from officials.
What makes swatting dangerous?
Swatting is a highly dangerous prank that comes with serious consequences. This is because the victim is usually unaware of the situation, and the response team is deployed thinking that there has been a very serious situation. In fact, there have been swatting incidents where the response teams and victims have been accidentally hurt or have been shot and killed. So it is crucial that swatting is taken seriously.
Furthermore, swatting also occupies a response team’s time, making them unavailable to respond to other real emergencies that are happening.
In more recent years, swatting has continued to be a larger issue due to advancements in technology. Specifically, it has made it harder for law enforcement to find the person who made the hoax call. These individuals are using more sophisticated techniques to hide their identity, with techniques like ID spoofing and voice changers to divert from their original number, make it appear as if they are a local caller and make it hard to recognize their identity. This means that a swatter can place a hoax call from anywhere in the world.
Who are victims of swatting?
Anyone can be a victim of swatting, but most known incidents have targeted people in the online gaming community, particularly those taking part in gaming live streams. This is because the attacker is able to watch the events unfold live. There have also been celebrities that have been targeted by swatters and other high-profile individuals such as politicians or board executives. Learn more about the personality types of cyber victims here.
Swatting Examples: How does swatting work?
Unfortunately, swatting can be simple to carry out. The attacker will first learn your home address through various techniques. This includes following paper trails but more commonly, using social engineering techniques. Attackers with more technical knowledge can track down your IP address to reveal your general location and combine it with other information they have dug up to track your specific location. They use all the information they find about you online, including your name, photos, public contact information, etc. Here are some of the ways they can trace you:
Social Media Usage
Attackers can stalk your social media profiles, where you may include details of your whereabouts, photos of your house, tagging nearby locations or the public friends you tag. Although many users are now becoming more aware of what they share online, there may still be some personal details that slip through the cracks.
Doxing
Doxing refers to when another attacker publishes all your personal information online with malicious intent. This includes very sensitive information such as where an individual might live and work, phone numbers, real names, and other records. Crucially in doxing, this information was not publicly available before. You can learn more about doxing here.
A swatter can easily find or come across this information and use it.
Phishing
Phishing is a type of social engineering technique that is used by attackers to get hold of your email address, phone number or other personal details. A swatter may use a phishing technique, where they pose as customer service agents, to get information that they need. Swatters can also send you malicious links to infect your device with spying malware.
After finding out your location, the attacker will then hide or spoof their information and ID before calling the authorities to create a hoax report that will elicit an emergency response. Unfortunately, there are now several examples of swatting you can find, but one of the most popular and well-known swatting cases is from the United States: The 2017 Wichita swatting.
A notable example of swatting
In 2017, Shane Gaskill and Caset Viner got into a heated argument during gameplay, in which Viner threatened to kill Gaskill. Gaskill provided Viner with a random address that was not his own, but in fact, belonged to an innocent bystander Andrew Finch. Viner later hired a serial swatter, Tyler Barris to place a false claim of a hostage situation at the address. A response team was dispatched and unfortunately, shot and killed Andrew Finch. Barriss, Gaskill and Viner were later arrested. This is probably the most high-profile swatting event to date.
Why is swatting happening?
Swatting most commonly grows out of a petty feud between individuals. Many swatting victims are streamers or gamers and come from attackers who seek revenge for being disrespected, defeated or humiliated within a computer game.
Attackers use swatting to cause irritation, inconvenience and fear for victims. In many cases, victims will feel extremely anxious and unsafe in a location. Sometimes, swatters may make these hoax calls repeatedly to create maximum disruption. Swatting is a type of abuse and harassment and doesn’t necessarily happen at a home address. It can also happen in a workplace, a school, or other frequently visited addresses by victims.
How to prevent swatting?
Once in motion, it can be difficult to stop, so the best way is to prevent it from happening and avoid becoming a victim. Here are a few simple processes and best practices to prevent swatting and protect your data:
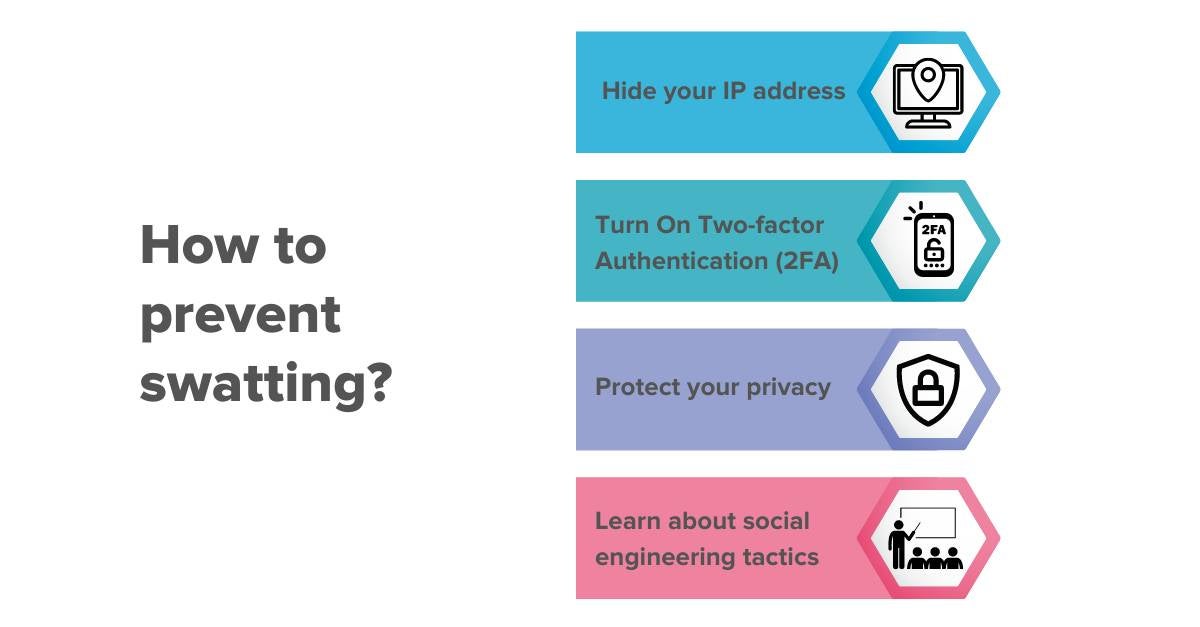
1. Hide your IP address
Every time an individual connects online, there is a wealth of information being transmitted without their knowledge, including real-time locations. To prevent this, it's recommended to disguise your IP address and use a VPN to route all your online traffic through remote servers, making it difficult for attackers to see where you are.
2. Turn On Two-factor Authentication (2FA)
Passwords alone are no longer enough to be safe. Secure your online accounts using two-factor authentication. This allows you to have additional security when you log into your personal accounts and devices. This makes it difficult for hackers to get into your accounts to find your personal information.
3. Protect your privacy
Individuals should protect their privacy and make it harder for attackers to get personal information by:
- Ensuring your name and address don’t appear on public spaces and social media sites
- Don’t trust people online with your information
- Enforcing strict privacy and security settings on all your profiles and devices
- Use nicknames or pseudonyms for accounts, and try to also use different names for different accounts
- Don’t post personal information. Once it's on the internet it is impossible to remove
4. Be educated about social engineering tactics
Threat actors are constantly evolving in their techniques. Staying informed on the latest social engineering schemes and tactics can ensure that you don’t fall victim to them. Organizations and individuals should also consider investing in software to help protect against social engineering scams.
Many of these tips are basic cyber security strategies as swatting is not the only threat individuals face online. Organizations and individuals should stay vigilant and ensure their cyber security practices are robust and up-to-date.
What to do if you are being swatted?
Although unlikely, if you find yourself to be a victim of swatting it is imperative to stay calm and cooperate. SWAT teams believe they are responding to a serious emergency, making it a high-stakes situation. Any sudden movements or actions can be interpreted adversely. Remaining calm will mean that authorities respond in the same manner.
It is also important to report any threats of swatting. This will help prevent any future swatting and save resources as response teams will have a record if dispatched that this may be a hoax.
Sangfor Solutions
Sangfor Technologies is a leading global vendor of IT infrastructure solutions, with a wide range of products & services, including systems to safeguard privacy and protect against becoming a victim. You can browse our service offerings, such as Next-Generation Firewall, Internet Access Management, Endpoint Protection, and Anti-Ransomware. If you would like to learn more about Sangfor's products, please feel free to get in touch with us.





