What is a Whaling Attack?
A Whaling Attack, also known as whaling phishing, is a cyberattack that focuses on important individuals within a company. These individuals typically include executives and key decision-makers. As a specific type of phishing attack and spear phishing attack, whaling aims at these "whales" of the corporate world.
Who are the Targets of Whaling Phishing Attacks?
Just as the name suggests, the main targets of whaling phishing attacks are the whales of the corporation. They are typically high-profile individuals within an organization who have access to sensitive information or can authorize significant financial transactions. These individuals are often:
- Executives: High-ranking executives such as CEOs, CFOs, and CTOs, are key targets for whaling cyber attacks. This is because of their powerful status in the organization. Their access to financial data, decision-making authority, and potential influence within the organization are what make them whales, the targets of this kind of attack.
- Board Members: Another vulnerable target of whaling attacks is the members of the board of directors or advisory boards. These members have significant influence over the organization's direction. Attackers often trick them into approving fraudulent transactions or revealing strategic information.
- Finance and Accounting Staff: Employees responsible for financial transactions, such as accounts payable and accounts receivable personnel, are often targeted. This is because of their ability to initiate payments or transfer funds on behalf of the company.
- Human Resources (HR): The HR department is a treasure trove of personal information. Whaling attackers target HR personnel for access to sensitive information of employees, such as including payroll data. This information is often used to carry out further attacks such as identity theft.
- IT Department: Staff in IT departments such as network administrators, are targeted to gain unauthorized access to IT systems. Through this access, attackers can make further attempts such as deploying malware within the organization's network.
Why is a Whaling Attack also called CEO Fraud?
Whaling attacks are popularly known as CEO fraud. This is because they often impersonate the CEO (Chief Executive Officer) of an organization specifically. A CEO often holds the highest authority in a company, making them the ultimate whale.
Their power regarding financial transactions, data access, and other sensitive actions is what attackers aim to manipulate. In addition, employees are more likely to trust and follow instructions seemingly coming from the CEO. As a result, it makes them more susceptible to attack.

How does a Whaling Attack Work?
- Step 1: Target Identification. Whaling attackers identify a high-value target, often a senior executive or someone with significant access to sensitive company information. The targets are usually CEOs, board members and so on.
- Step 2: Research on the Target. Once a target is identified, attackers carry out elaborate research to gather information about the target, including their responsibilities, contacts, and behavioural patterns. This information helps in crafting a convincing attack.
- Step 3: Impersonation. With all the information, the attackers impersonate someone the target executive knows and trusts. It includes another high-level colleague, a business partner, or even a fake internal IT support person.
- Step 4: Social Engineering Attack. They craft emails or phone calls using social engineering tactics to create a sense of urgency, importance, or confidentiality. For instance, these emails might say they're about a secret business deal, an important money issue, or a crucial decision needing quick action.
- Step 5: Tricking the Victim. Now the victim is tricked into taking some action, which is beneficial to the attacker. Most common actions include sharing sensitive information like login credentials or financial data, authorizing a fraudulent wire transfer, or clicking a malicious link that downloads malware onto the executive's device.
Real-Life Whaling Attack Examples
Ubiquiti Networks
On June 5th, 2015, Ubiquiti Networks discovered that it fell victim to a whaling attack. The attack targeted an employee in the company's Hong Kong subsidiary finance department. The cybercriminals impersonated company executives sending spoofed emails and tricked them into transferring approximately $46.7 million to fraudulent accounts.
Upon discovery, Ubiquiti Networks managed to recover $8.1 million of the stolen funds. An additional $6.8 million is subjected to legal injunction and is expected to be recovered. After the attack, Ubiquiti Networks enforced stringent control over financial reporting.
Mattel
In 2016, the toy company Mattel suffered a whaling attack. A high-ranking financial executive received a fraudulent email from someone posing as the newly posted CEO, Christopher Sinclair. The email requested a new vendor payment of $3 million to a Chinese supplier.
The payment was processed to the Bank of Wenzhou before the scam was discovered. Fortunately, as it was a banking holiday on May 1st, Mattel could contact authorities and freeze the account before the attackers could access the funds.
Seagate Technology
In 2016, the data storage company, Seagate Technology was targeted by a whaling attack that led to the disclosure of employee information. The attackers posed as the company's CEO and CFO, requesting sensitive employee data, including W-2 tax forms. As a result, around 10,000 current and former employees' personal information such as social security numbers was compromised.
Later, the company faced a class-action lawsuit from affected employees accusing the company of malpractice, lack of surveillance, and poor handling of sensitive data.
Facebook and Google
In 2017, it was reported that a Lithuanian man named Rimasauskas orchestrated a whaling cyber attack against two tech giants, Facebook and Google. He impersonated a legitimate vendor called Quanta Computer and tricked the companies into wiring over $100 million to his bank accounts.
The scam was discovered, and the perpetrator was arrested and charged. The two companies recovered most of the funds, whose exact figures remained undisclosed.
Snapchat
In February 2016, a whaling attack on Snapchat targeted a high-ranking employee in the company's payroll department. The attack impersonated the CEO and deceived the employee into revealing payroll information about some current and former employees. It included sensitive details like financial data and stock options.
The company reported the incident and FBI and offered two years of free identity-theft insurance and monitoring to the affected employees.
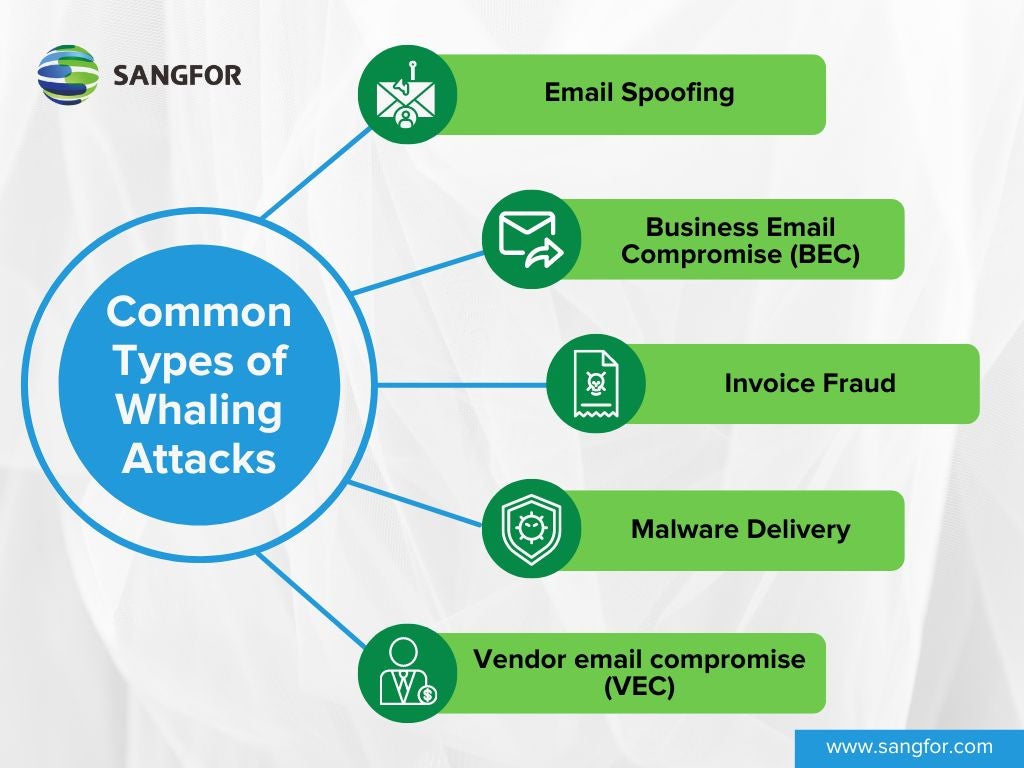
Common Types of Whaling Attacks
Some of the most common methods through which whaling attacks enfold are as follows:
- Email Spoofing: The most common type of whaling attack is spoofing the email address of a high-ranking executive. Cyber criminals make it appear as though the email is coming from a legitimate source within the organization. The email may request sensitive information, initiate a fraudulent financial transaction, or trick the recipient into clicking on malicious links or attachments.
- Business Email Compromise (BEC): Also known as CEO fraud, BEC involves impersonating a CEO or other top executive to deceive employees into taking actions that benefit the attacker, such as transferring funds to a fraudulent account or disclosing sensitive information.
- Invoice Fraud: In this invoice fraud, attackers send fraudulent invoices that appear to come from trusted vendors or business partners, which may have worked for targeted companies previously. The email with invoice might pressure the executive to authorize payment quickly to avoid disrupting operations or incurring late fees.
- Malware Delivery: Whaling email may embed malicious links or attachments. Clicking on these can download malware onto the victim's device, potentially granting the attacker access to the company's network or sensitive data.
- Vendor email compromise (VEC): In this kind of whaling cyber attack, the cybercriminals impersonate the vendors or suppliers of an organization. They send out realistic emails such as sending fake invoices, requesting unauthorized payments, or redirecting legitimate payments to fraudulent accounts.
Whaling Phishing Examples
Common whaling phishing examples include:
- Sends an email impersonating a trusted vendor or business partner, requesting urgent payment for an invoice.
- Impersonating a CEO or senior executive to instruct employees to perform tasks such as wire transfers.
- Scammers send emails pretending to be from the board of directors, setting up fake meetings with malware.
- Attackers intercept an ongoing email conversation between a CEO and a vendor and inject a fake email requesting bank transfers.
How to Recognize a Whaling Email?
As a whaling email is realistic, recognizing it requires careful attention to detail and awareness of common characteristics of such attacks. Here are some tips to help you recognize a whaling email:
- Sender's Email Address: Check the sender's email address carefully. Whaling emails often are sent with misspelt names, unusual domain extensions (e.g., ".top" instead of ".com"), or slight variations of a legitimate email address (substituting "rn" for "m" to appear like a real address).
- Urgency and High Pressure: Whaling emails often create a sense of urgency or high pressure to prompt immediate action. Watch out for emails demanding immediate action or claiming critical consequences for delays.
- Unusual Requests: If an email asks you to do something unusual, especially involving financial transactions or sharing sensitive data, be suspicious. Double-check with the sender through a trusted communication channel like a phone call to verify the request.
- Generic Greetings: Whaling emails may use generic greetings like "Dear Sir/Madam" or "Dear Customer" instead of addressing you by name implying a mass phishing attempt. Legitimate emails from within your organization are more likely to use your name or a personalized greeting.
- Spelling and Grammar Errors: Pay attention to spelling and grammar errors in the email. Legitimate emails from professional organizations typically have correct spelling and grammar. While whaling emails include grammatical errors or typos often because of hastily crafted phishing attempts.
- Suspicious Links and Attachments: Even if the email seems fully legitimate, avoid clicking on links or downloading attachments from it. Whaling emails may contain links to malicious websites or attachments that can infect your computer with malware.
Whaling Vs. Phishing Vs. Spear Phishing
| Aspect | Whaling Attack | Phishing Attack | Spear Phishing Attack |
|---|---|---|---|
| Target Audience | High-profile individuals within an organization | A wide range of individuals, including employees, customers, or general users | Specific individuals or groups targeted based on research and personalized information |
| Goals | Financial fraud, data theft, or unauthorized access | Stealing login credentials, financial information, personal data, or installing malware | Gaining access to sensitive information or systems |
| Level of Targeting | Highly targeted | Broadly targeted | Highly targeted |
| Level of Personalization | Highly personalized emails with specific details about the target | Low-level generic emails | Medium emails tailored to a specific group or department |
| Potential Impact | Significant financial loss, data breaches, reputational damage | Identity theft, financial loss | Compromised department data or systems |
| Example | Email impersonating the CEO requesting an urgent wire transfer | Email claiming to be from your bank asking for login details | Email disguised as an IT notification targeting the finance department |
| Mitigation Measures | Employee training, strict verification processes, and email authentication protocols | Employee training, spam filters, email authentication protocols and so on | Employee training on social engineering, multi-factor authentication, and continuous monitoring for suspicious activity |
How to Protect Yourself from Whaling Phishing Attacks?
Preventing whaling attacks requires efforts both on the individual level and organizational level.
Individual level
- Be sceptical: Individuals should not assume any email, even from a seemingly familiar address, is legitimate. Everyone must be wary of emails, especially those requesting urgent action or sensitive information.
- Verify sender information: The most important step is to examine closely the sender's email address. Whaling emails often have subtle typos or use a slightly different domain name than the real sender but are nearly similar.
- Hover over links before clicking: Even if there are errors in the email address or content, users must look at the true destination URL when they hover their mouse over a link. Always remember not to click on links that lead to suspicious websites.
- No sharing via email: Even if the email seems legitimate, individuals should never share sensitive information like passwords or financial data.
- Report suspicious emails: Even if everything seems right, yet your gut says otherwise, always report them to your IT department or security team.
Organization Level
- Educating employees: Organizations must train employees on how to identify phishing attempts and what to do if they receive a suspicious email. They must implement regular employee training on whaling attack recognition, especially those in high-profile positions.
- Multi-factor authentication (MFA): As MFA adds an extra layer of security, organizations must enforce it, when logging into accounts or making financial transactions.
- Using anti-phishing software: This software can help identify and block phishing emails before they reach employees' inboxes, thereby reducing the probability of falling victim to whaling attacks.
- Email security: Enterprises must configure efficient email filters to flag suspicious emails and restrict attachments from untrusted sources.
- Software update: Organizations must ensure all devices and software are up to date with the latest security patches to close vulnerabilities, thereby blocking any leeway to whaling attempts.
- Monitor third-party vendors: One must ensure that third-party vendors follow strict security protocols to prevent breaches that could lead to whaling attacks.
- Data protection software: Even if there has been a whaling attempt, organizations should prepare themselves to prevent any data loss. They must implement data protection measures to safeguard sensitive information and detect unauthorized access.
- Caution on social media: High-profile individuals should pay attention to what they share on social media as criminals could use in whaling attacks by the criminals.
Cyber Protection with Sangfor
Sangfor offers a range of cutting-edge cyber security products designed to effectively combat ransomware threats:
- Sangfor Network Secure: This NGFW solution provides comprehensive protection against known and unknown threats. It also integrates with Sangfor’s AI-powered Engine Zero for advanced threat detection and prevention.
- Sangfor Endpoint Secure: This endpoint security platform (EPP) offers robust endpoint protection, continuously monitoring and defending against ransomware attacks. It uses machine learning to detect and block malicious activities before they can cause damage.
- Sangfor Cyber Command: An advanced threat detection and response platform that provides real-time visibility into network traffic and user behaviour. It Identifies and mitigates ransomware threats quickly, preventing lateral movement within the network.
- Sangfor Omni-Command XDR: An Extended Detection and Response platform delivering a unified, intelligent, and proactive approach to threat detection and response. It integrates seamlessly with other Sangfor products to provide comprehensive protection across your entire IT infrastructure.
- Sangfor Anti-Ransomware Solution: Sangfor’s Anti-Ransomware Solution is specifically designed to protect organizations from ransomware attacks by employing a multi-layered defence strategy. It works on four pillars of prevention, detection, response and recovery.
Also, watch the “Stop Ransomware in 3 Seconds” video for a quick overview of how Sangfor safeguards your digital assets against ransomware with lightning speed.
If you want more information on any of our solutions, visit us at www.sangfor.com or connect with us.
Frequently Asked Questions
A whaling attack is a type of cyberattack that targets high-profile individuals, typically CEOs, CFOs, or other executives within an organization.
While both whaling and phishing are forms of cyber deception, whaling specifically aims at the ‘big fish’ or high-ranking executives of an organization. Phishing attacks, on the other hand, are more general and can target anyone.
Whaling attacks' other names are CEO fraud, executive phishing or spear phishing.
In 2016, attackers launched a whaling campaign against executives at Ubiquiti Networks, a tech company. They impersonated the CEO and sent emails requesting employees to transfer funds to a fraudulent account. The attackers stole millions of dollars before the scheme was discovered.
The goal is typically to extract sensitive information such as employee payroll information or to initiate unauthorized financial transactions.
High-ranking individuals within organizations, such as executives and senior managers' job titles, are the primary targets.
Users, especially high-profile individuals must be cautious of emails, even if they appear to come from someone familiar. Always, verify the sender's identity by phone or another trusted channel before taking any action. Organizations should implement security awareness training for employees to educate them about these attacks.





