The world is quickly changing and digital landscapes are constantly advancing. This makes it important to understand the new threats that are out there. Cyber-attacks are becoming more sophisticated each day. The role of cryptocurrency in ransomware is now being explored a lot more.
What Is Cryptocurrency?
Unless you’ve been living under a rock, you’ve probably heard of the term cryptocurrency before. Cryptocurrency is a form of digital money that can be exchanged for goods or services online. The major difference between “crypto” and real money is that cryptocurrency is not issued by a central authority.
Companies – like Bitcoin, Cardano, and Ethereum – all have specialized forms of currency called “tokens” which can be used to trade or be exchanged for real money. Bitcoin was the first cryptocurrency created - and is now the most valuable and popular version. Launched in 2009 by Satoshi Nakamoto, Bitcoin immediately took off.
The Bitcoin supply was capped from the beginning by Nakamoto. The maximum number of coins stipulated to be in existence was 21 million. As of May 10, there were 19.36 million Bitcoins in existence. However, Bitcoin's value decreased more than 70% from its all-time high of US$ 68,990 in November 2021 before rebounding sharply in the first half of 2023.
Cryptocurrency companies use something called “blockchain technology” to spread across many different computers that manage and record transactions. Each transaction made forms an unbroken link on the chain. This transparent, public chain is what allows Bitcoin to exist and be usable.
The popularity of crypto peaked due to the highly secure and anonymous nature of the medium. However, that same difficulty to trace is also what made it an attractive choice for many cybercriminals.

Cryptocurrency Fuels Ransomware
Ransomware attacks have become increasingly popular these days and hackers are now finding it more convenient to use cryptocurrency platforms to get away with it.
In a typical ransomware attack, a victim’s files or data are stolen and encrypted. The hacker then reaches out with a ransom demand – using the threat of exposing the stolen data as leverage. After paying the ransom, a key is then given to the victim to decrypt the data.
Now while you might imagine a ransom situation with money being stuffed into a duffel bag and left in an abandoned alleyway, hackers have proven to be a lot more sophisticated these days.
With the use of cryptocurrency, cybercriminals can automatically transport large amounts of money across international boundaries within seconds. The lack of trackability and ease make this the ideal way to demand a ransom.
Bitcoin has been in the headlines numerous times due to hackers using the medium to extort money from victims. One of the most famous cryptocurrency ransomware attacks includes the WannaCry ransomware attack of 2017. The attack infected an estimated 200,000 computers in 150 countries across the globe.
The attackers initially demanded $300 in Bitcoin to unlock infected computer systems. The demand was later increased to $600 in Bitcoin. Victims were told that if the ransom was not paid within three days, their files would be permanently deleted. Some researchers still claim that no one got their data back - even if they met the demands.
In 2013, CryptoLocker disarmed more than 250,000 computer systems. Victims were instructed to send payments in cryptocurrency or money cards to regain access. The ransomware delivered at least US$ 3 million to its perpetrators.
In more recent news, Mikhail Pavlovich Matveev was charged by US authorities for his alleged connection to multiple ransomware schemes. These attacks earned him and other attackers almost US $200 million – much of which came through the use of crypto.
Why cryptocurrency Is Used in Ransomware
According to the Wall Street Journal, hackers that request payment in the form of cryptocurrency can be “difficult to pursue across digital wallets and national borders.” These exchanges also typically take place overseas which limits governmental regulatory power and law enforcement.
Coin Center director of research, Peter Van Valkenburgh, also wrote in 2017 that the efficiency of cryptocurrency networks - rather than their secrecy – is what attracts hackers.
It’s electronic cash, so it’s easy to write software that can automatically demand payment and automatically demand that payment has been made.
Peter Van Valkenburgh, director of Research at the Coin Center
Additionally, the majority of ransomware attacks these days are carried out by hackers offering “ransomware-as-a-service”. Essentially, you pay these cybercriminals to hack a specific person or network for a fee – which is naturally paid through cryptocurrency.
Cryptocurrency can also be used for other forms of cyber-attacks. Cryptojacking hijacks the victim’s computer resources to mine cryptocurrencies. The code typically works quietly in the background as unsuspecting victims use their systems normally. The only signs they might notice are slower performance, lags in execution, overheating, excessive power consumption, or abnormally high cloud computing bills.
Punch publication recently revealed a report that showed “miner malware is often the harbinger of other malware, as it is usually deployed via easily exploitable network and software vulnerabilities.”
Cryptocurrency also makes it easier for the hacker to see exactly when the ransom has been paid due to the transparency of the exchanges.
While the threat is increasing, pressure is constantly being put on lawmakers to protect the public from being exploited in this way. In 2021, several senators and representatives sent a letter to the Departments of Justice, State, and Homeland Security urging them to address – among other things – the role of cryptocurrencies in the rise of ransomware attacks, noting the anonymity the digital currencies give attackers.
Peter Van Valkenburgh, the director of Research at the Coin Center, also told IBT that it’s quite likely that law enforcement agencies will be able to track down the attacker even if the culprit doesn't exchange the extorted bitcoins for dollars.
Methods to deanonymize Bitcoin transactions have already been published at the University of Luxembourg. This helps to reassure the public that the relevant authorities can still be relied on to track ransoms.
The US Homeland Security and Governmental Affairs Committee released a report that stated “The use of cryptocurrencies has further enabled ransomware attacks, particularly because cryptocurrency is decentralized and distributed and illicit actors can take steps to obscure transactions and make them more difficult to track.”
According to the report, malign actors received at least US$ 692 million in 2020 in the form of cryptocurrency extorted as part of ransomware attacks - up from US$ 152 million in 2019.
The report further states that for multiple agencies interviewed by Committee staff, cryptocurrency - specifically Bitcoin - has become a nearly universal form of ransom payment in ransomware attacks, in part, because cryptocurrency enables criminals to extort huge sums of money from victims across diverse sectors with incredible speed.
On March 9, 2022, the Biden Administration issued an Executive Order outlining a “whole-of-government” approach to examining the risks associated with the sharp increase in the use of cryptocurrencies.
However, government and legislature can be slow to act – especially when the digital landscape of crypto is difficult to properly understand in the first place. This means that people have to take steps to protect themselves and their businesses on a personal level.
How to Protect Your Business from Ransomware
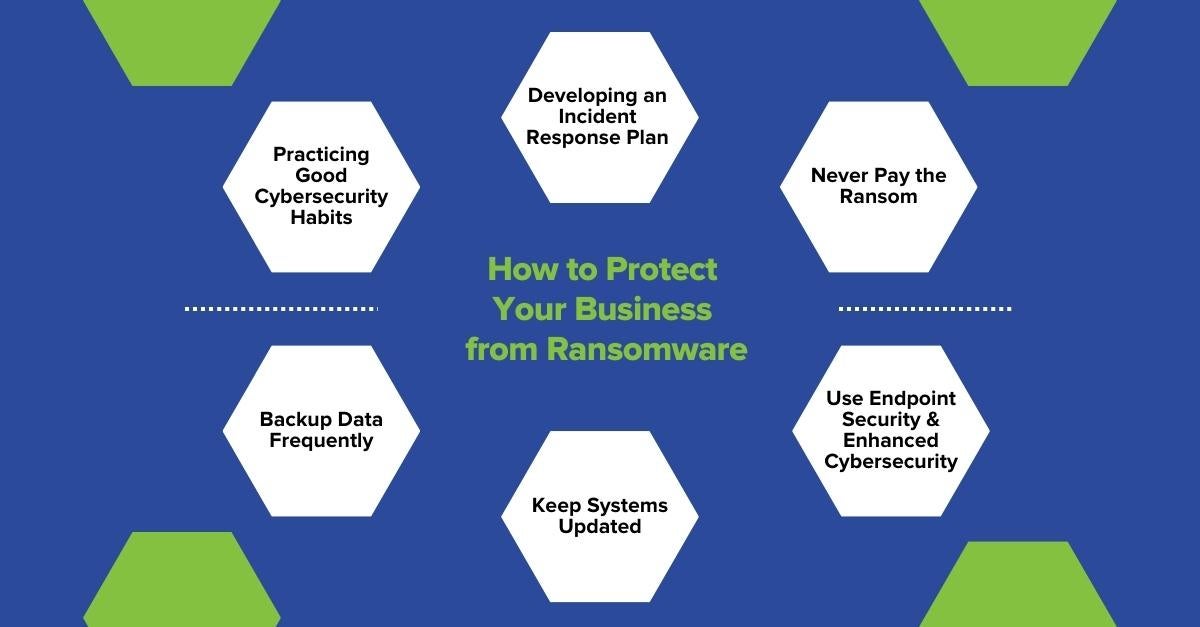
It’s important to protect yourself and your business from ransomware attacks in every way possible. Here are some easy steps to ensure ransomware protection:
Practicing Good Cybersecurity Habits
It is important to ensure that you and every person in your organization make use of adequate cyber hygiene practices. These are a basic set of exercises that will improve and maintain cybersecurity. This includes regular workshops, training exercises, and daily cybersecurity upkeep to ensure that your network is protected.
Developing an Incident Response Plan
Be prepared in the event of a ransomware attack by ensuring that your company has an incident response plan ready to go. This will help to minimize damage and financial loss.
Never Pay the Ransom
While it might seem easier to simply pay off the hackers, there is no guarantee that your information will be safe or returned to you once the payment is made. Especially if you’re using cryptocurrency to pay the ransom.
Backup Data Frequently
Your data is usually at risk when your company does not have adequate backup systems in place. Ensure that all your data is backed up and secure. This will guarantee all sensitive business and client data is safe, and that you can resume operations seamlessly.
Keep Systems Updated
Your network is mostly at risk when your software is outdated. Ensure that your systems are always updated and that all vulnerabilities are patched to avoid being a victim.
Use Endpoint Security
Your endpoints are typically the weakest spot in your network. This makes them the ideal target for hackers. Ensure that your company uses an Endpoint security solution designed to help protect each endpoint connected to your network. These include laptops, servers, smartphones, printers, and more.
Use Enhanced Cybersecurity
Your security is only as good as your security provider. Sangfor’s Next Generation Firewall (NGFW) can be used in conjunction with Endpoint Security to identify malicious files at both the network level and endpoints. The advanced firewall is a security device designed to inspect network and application traffic for threats, secure the network environment from intrusion, and bring in security intelligence from outside the network.
Additionally, Sangfor’s Cyber Command (NDR) Platform constantly monitors for malware, residual security events, and future potential compromises in your network. The solution is coupled with Threat Intelligence and an enhanced AI algorithm to keep you updated with any vulnerabilities in the system while ensuring your data is always kept strictly protected and consistently monitored for lingering threats.
Sangfor Technologies is a leading and trusted cybersecurity and cloud computing provider that makes use of intelligent design and innovative thinking to ensure the best protection for your company. There are multiple other ways to protect your company from ransomware in 2023 and investing in the right cybersecurity provider should be your priority.
For more information on Sangfor’s cyber security and cloud computing solutions, visit www.sangfor.com.





