October is celebrated as Cybersecurity Awareness Month; focusing on the basics of Cyber Security that every individual and companies need to take care of. This is our another article inline with that initiative.
The modern age has brought about several extraordinary developments in technology. However, with our rapid ascent into an era of innovation, we have a responsibility to maintain and protect the digital transformation we push ourselves into achieving.
The surface area for cyber-attacks has dramatically expanded in the last two years with the rise in remote and hybrid working environments and now people are finding themselves falling victim to even more sophisticated cyber threats than ever before – which begs the question, what can we do to improve how we navigate cyberspace to ensure that we are not also victims?
As the tide turns on technology and we strive towards new and more exciting territories, we have to remember the fundamentals of keeping our cyberspaces clean and focus on improving our cyber hygiene practices to stay protected.
What Is Cyber Hygiene?
Cyber hygiene is the basic set of exercises that every computer or internet user agrees to fulfill in order to improve and maintain perfect cyber health. It’s from the way we extend precautions online with our sensitive information to the way we update the security software on our PCs. The term is much like personal hygiene, which staves off viruses and bacteria which can make us sick – only this time your immune system is computer software and the infections slowing you down are a bit more complicated.
Cyber safety is becoming a growing concern and companies are now focusing on how exactly they can improve their cyber hygiene to maximize their organization’s cyber protection. Expanding on cyber hygiene means adopting habits and protocols that are centered around cybersecurity.
Each time we use the internet, we open ourselves up to a multitude of cyber-attacks that threaten our safety.

Why Do We Need Better Cyber Hygiene Practices?
A recent study by Ernst & Young has revealed that employees from younger generations – who make up a significant portion of the workforce – are less likely to prioritize or even adhere to their employer’s cybersecurity protocols. When cyber safety is not regulated and cyber hygiene practices are not observed, entire organizations can fall victim to different malware and ransomware attacks - which can affect entire sectors on numerous fronts:
Data Protection
A recent attack aimed at the Shangri-La hotel chain in May led to a significant data breach that affected guests and bookings at the hotel. Comparable to the IHG hotel chain cyber-attacks that ended with sensitive information being accessed, operations disrupted and data destroyed, the Shangri-La breach shows how crucial cybersecurity measures are. The implementation of better cyber hygiene could have ensured that the hackers were stopped before any sensitive information could be accessed and any operations were halted.
Supply Chains
The notorious Colonial Pipeline ransomware attack easily shows the ripple effects across supply chains that ineffective cyber safety protocols can have after a cyber-attack. The biggest refined products pipeline in the US discovered ransomware in May of 2021 and shut down operations – affecting airlines, inflation rates, and forcing job losses. Many other cyber-attacks have had similar effects on supply chains as well. Stronger ransomware protection in place would have prevented those effects if cyber hygiene conventions were taken more seriously.
Food Resources
Supply chain disruptions also lend to the food resource supply line, which can just as easily come under fire. The world’s largest meat processing company proved this in May of 2021 when JBS shut down operations across the USA, Australia, and Canada after becoming victims of a ransomware attack. This affected operations, jobs, and the price of meat for all those dependent on the nationwide industry supplier.
Crypto Security
The latest cyber-attack on Binance can be used as an example of lacking cyber hygiene. This past week, the largest cryptocurrency exchange revealed that hackers were able to exploit a flaw in the BNB blockchain - allowing them to mint 2 million BNB tokens worth an estimated US$570 million. The company assured the public that it would be implementing cybersecurity upgrades to prevent this from happening again.
Government Operations
Finally, and perhaps the most sinister of all cyber-attack repercussions, are those that occur within higher levels of government – where the aftermath can extend to entire countries and have devastating consequences for millions. This was seen in the state of emergency declared by the Costa Rican President after the Conti ransomware attack threw the country into chaos in April of this year. The attack affected healthcare systems amid covid-19 testing and will likely have lasting effects on the country.
So now that we know how the neglect of cyber hygiene practices can wreak havoc, how do we go about adopting those much-needed steps into our organizations?
How Can We Introduce Effective Cyber Hygiene?
According to the US Cybersecurity and Infrastructure Security Agency, there are proactive approaches that one can take to avoid the risk of cyber-attacks instead of simply fortifying systems alone:
Vulnerability Scanning
This involves the continuous scanning of external public IPs for any suspicious behavior or vulnerabilities – the process helps to find weak spots in the system and uses specialized tools to create an inventory of known and acceptable software to contrast against any foreign ones found inside the database. The automated reports generated by vulnerability scanning ensure that your data and system are protected at all times.
Web Application Scanning
The inspection of accessible public websites is done by this integral feature in your cyber hygiene routine. The web application scanner will search any website accessed for potential bugs, weak configurations, or any vulnerabilities during user interface and report back any threats that might corrupt your network.
Cybersecurity Experts
Additionally, one can rely on the expertise of professionals in the field to provide advanced Threat Identification and Risk Assessment (TIARA) capabilities for your network – a service that provides preliminary security assessments that are designed to help customers identify threats to their network in a short period.
Carnegie Mellon University focuses on the risk factor involved in implementing effective cyber hygiene, stating that good cyber hygiene involves identifying, prioritizing, and responding to risks to an organization's key services and products.
They also list 11 practical baseline practices to manage cybersecurity risks for organizations
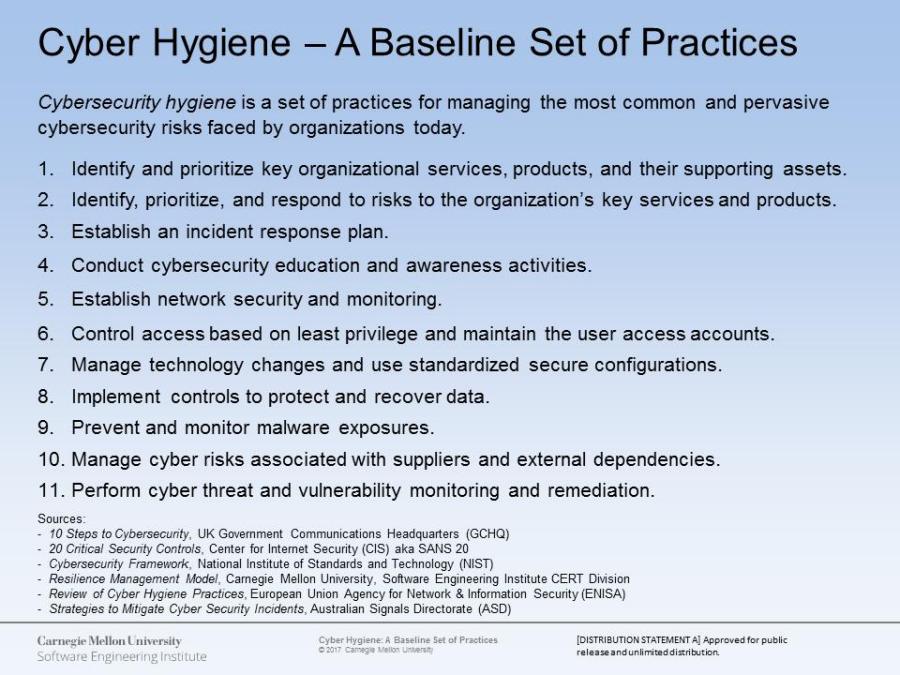
Sourced from the Carnegie Mellon University blog on “Cyber Hygiene: 11 Essential Practices”
Cyber Safety
The establishment of cyber hygiene practices and protocols is meant to be leading to a state of ultimate cyber safety for all organizations to inculcate and emulate. These strategies can be seen as an essential part of any company’s digital infrastructure and are secure in that role by the active campaigning of governing bodies for more advanced and stricter cybersecurity controls and awareness. A move that was amplified by US President Joe Biden’s call for better cybersecurity.
Cybersecurity Awareness Month
The United States declared October to be Cybersecurity Awareness Month to educate the public, and private sectors, of the dangers lurking around in cyberspace and the duty of companies and ordinary people alike to engage with and establish lasting cybersecurity practices.
The Department of Homeland Security, in cooperation with the National Cyber Security Alliance and the Multi-State Information Sharing and Analysis Center, left the message that cybersecurity and keeping the internet safe for everyone is a shared responsibility.
The “See Yourself in Cyber” toolkit reiterates this message and focuses on the need to create a safer online environment for us to enjoy together.
A key element for any company looking to invest in better cybersecurity and to endorse better cyber hygiene in their organization is to look for a provider that focuses on protection and innovation and Sangfor Technologies is precisely that type of cybersecurity vendor.

Source: America's Cyber Defense Agency
Sangfor’s Solutions for Better Cyber Hygiene
Sangfor strives to provide pioneering and versatile cybersecurity solutions for your company to ensure that advanced cyber hygiene is always upheld and effective cyber resilience is always maintained.
We understand the threats that are out there and we know how to keep your organization safe with our range of unique, integrated, and enhanced solutions:
- The Sangfor Cyber Command (NDR) Platform helps to monitor for malwares, residual security events, and future potential compromises in your network and is coupled with Threat Intelligence technology and an enhanced AI algorithm to keep you updated on any vulnerabilities or threats detected in the system.
- In addition, our advanced Endpoint Secure technology provides integrated protection against malware infections and APT breaches across your entire organization's network – all with ease of management, operation, and maintenance. The platform also received the AV-TEST “Top Product” award for achieving 100% ransomware protection against zero-day malware.
- Sangfor’s Incident Response service is geared towards flexible, fast, and effective elimination and prevention of cyber-attacks. The focus of incident response is locating and eradicating threats while implementing active disaster recovery and providing tailored analysis to help safeguard your company from future cyber-attacks.
- Sangfor knows that an incident response plan must be put into place and also offers security assessment solutions to ensure your organization’s ability to recover for anything.
For more information on Sangfor’s cyber security and cloud computing solutions, visit www.sangfor.com.
Frequently Asked Questions
Cyber hygiene refers to a set of exercises and practices that users can adhere to to ensure that their data is safe and their computer system is protected from cyber threats.
The rising number of cyber-attacks across the globe has pushed many companies, and individuals, to reconsider their cybersecurity practices and focus on enhancing their safety. The risks outweigh the leisure of not doing anything.
No, organizations can easily maintain the necessary levels of cyber safety by investing in the appropriate cybersecurity measures suited to their needs and instilling proper cyber hygiene practices.





