Endpoint Detection and Response (EDR) is essential in today’s cybersecurity landscape, using AI and machine learning to monitor and analyze endpoint activities in real-time. This article delves into the basics of EDR, the expanding market, and some top open-source EDR tools, helping organizations bolster their defenses against sophisticated attacks and advanced cyber threats.
What are EDR Tools?
Endpoint Detection and Response (EDR) is a cyber security solution used to detect and respond to cyber threats on endpoints. EDR tools use AI and machine learning to continuously monitor and analyze endpoint activity in real-time, including all processes, files executions, network traffic, and user logins. This enables EDR tools to discover not only malware but also suspicious behavior that might indicate an advanced threat. Security teams are then alerted about the malicious activity for further investigation and manual response. EDR tools can also be configured with automated responses to remove and isolate threats from the network.
Security teams use EDR tools to simplify network security processes and free up time for more productive and business-centric tasks. Primary functions of an EDR solution include:
- Monitor traffic and data of endpoints in real time for anomalies or suspicious behavior that might indicate a threat or breach.
- Respond automatically by containing or removing all threats or malicious files. Alert security staff of their presence and risk to the network.
- Use behavioral analytics tools designed to research prominent threats and search for their signatures.
Anton Chuvakin, Gartner’s research director, coined the term “EDR” in 2013 while researching the need for more powerful malware hunting tools capable of “detecting and investigating suspicious activities (and traces of such) other problems on host/endpoints.” In short, EDR is dedicated to active threat detection and proactive threat hunting and is less focused on prevention, a vast deviation from traditional anti-virus.
How do EDR Tools Work?
EDR tools continuously monitor and analyze endpoint activities to detect and respond to potential threats. Here’s a brief overview of their functionality:
- Data Collection: EDR systems gather real-time data from endpoints, including processes, file executions, network traffic, and user logins.
- Behavioral Analysis: Use AI and machine learning to identify patterns and anomalies that may indicate potential threats and compromise IOCs.
- Threat Detection: Detect potential threats using behavioral analytics and threat intelligence.
- Alerting: Generate alerts for security teams with detailed threat information, enabling security teams to take swift action.
- Response: Automatically respond to threats by isolating endpoints, removing malicious files, or blocking traffic to reduce the attack surface.
- Investigation and Remediation: Enable security teams to investigate and remediate threats, performing root cause analysis and preventing future incidents.
- Continuous Improvement: Adapt and improve detection and response capabilities based on new threats.
By enabling proactive threat hunting and swift responses, EDR tools are essential for modern cybersecurity.

The EDR Security Solutions Market
The global endpoint security market is expected to reach $16.25 billion by 2024 and continue growing to over $36 billion by 2028. The EDR market is characterized by:
- The adoption of software-as-a-service (SaaS) or cloud-based endpoint security solutions is increasing due to scalability, lower costs, and lower operations and maintenance requirements.
- The number of endpoints is increasing, meaning the amount of sensitive data they access that could be at risk.
- Attackers are directly targeting endpoints to penetrate the network, avoiding traditional network defences.
- Endpoint security tools are being consolidated into a single endpoint protection platform (EPP) for enhanced security and easier management.
- Endpoint protection platforms (EPP) and EDR tools have been merging together for some time.
What are Open-Source EDR Tools?
Open-source Endpoint Detection and Response (EDR) tools are software solutions designed to monitor, detect, and respond to cyber threats on endpoints like computers and servers. Unlike commercial EDR tools, open-source options are freely available and can be customized to fit specific needs. Here are some key features and examples:
Top 5 Open Source EDR Tools
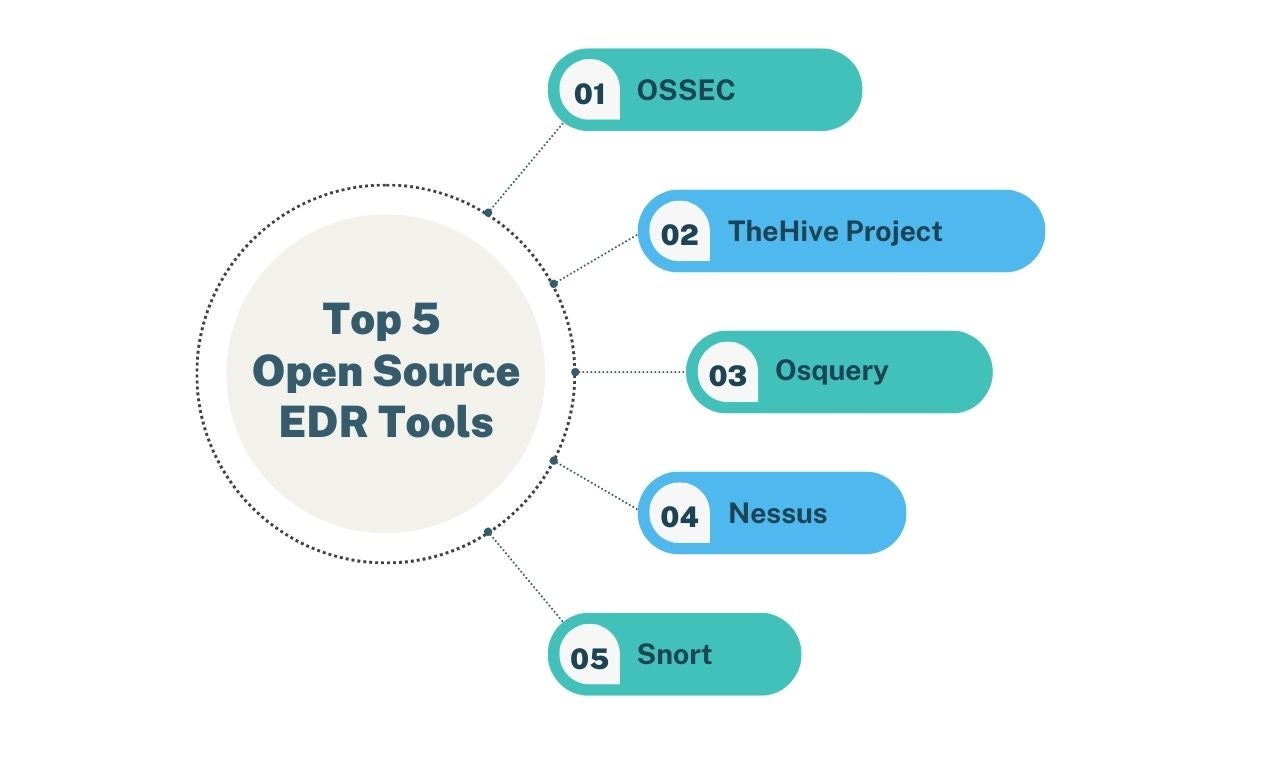
1. OSSEC
OSSEC is an open-source and free EDR software that offers log analysis, real-time windows registry monitoring, and other EDR features. OSSEC is primarily used in large enterprises, SMBs, and governmental agencies in need of light EDR functions. OSSEC provides:
- Endpoint scanning and analysis of log data coming from multiple endpoints.
- Malware and rootkit detection with process- and file-level scanning to detect malicious applications.
- Active response using firewall policy benchmarking and supports integration with 3rd party applications.
- System inventory retrieves data like listeners, hardware info, installed software, versioning, utilization rate, and network services.
2. TheHive Project
TheHive Project is a “security incident response (platform) for the masses,” drafting fast and detailed security incident reports to help inform security strategies. TheHive Project is a collaboration platform with powerful live streaming, real-time information, and task assignation. TheHive Project provides:
- Dynamic dashboard provides password protection for RAR and ZIP archives, importing zip archives containing suspicious data or malware, and custom templates.
- Advanced filtering options allow users to create custom alerts and provide filtering and easy export.
- Forensics and incident response means an overview of IPs, URLs, addresses, domain names, hashes, and files via a web interface.
- Cross-analysis of incident reports using web services like VirusTotal.
3. Osquery
Osquery is released as an application under the Apache license, with querying software that increases the visibility of connected devices. It is typically used by SMBs and large enterprises.
- Interactive querying console provides a comprehensive view of operating systems, helping users discover valuable data faster and easier.
- Powerful host-monitoring daemon aggregates query results to generate logs faster, helping track configuration, performance, and infrastructure health.
4. Nessus
Nessus vulnerability scanner scans ports for system vulnerabilities but does not have full EDR capabilities. Nessus provides:
- Custom scripting and multiple plugins with scripting language, server detection, processor information, recent file history, Windows scan performed without admin privileges, and Microsoft Windows last boot time.
- Patching indicator provides vulnerability detection and suggestions on how to fix or patch vulnerabilities.
- In-depth vulnerability scanning of up to 1,200 checks (passes) for system vulnerabilities.
5. Snort
Snort is robust intrusion prevention software designed to analyse packet logging and real-time traffic. It is a useful EDR tool for audits and threat investigations but does not have full EDR capabilities. Snort provides:
- Multi-mode deployment includes sniffer, packet logger, and NIDS (network intrusion detection system).
- Tunnelling protocol support for PPTE over GRE, MPLS, GRE, IP and ERSPAN.
Sangfor Endpoint Secure (EDR)
Sangfor Endpoint Secure is Sangfor's approach to meet with the best practices of EDR Solutions that go beyond traditional endpoint security solutions.
Endpoint Secure is integrated with Sangfor’s AI-powered malware detection engine, Engine Zero. It provides the most powerful and intelligent detection of advanced and unknown malware. Endpoint Secure also benefits from Sangfor’s Neural-X threat intelligence platform, which enables Endpoint Secure to capture the latest emerging cyber threats.
Sangfor Endpoint Secure is built with innovative anti-ransomware tools, including the world’s first and only endpoint ransomware honeypot. The honeypot uses decoy files to detect and kill the ransomware encryption process in real-time, minimizing any damage to the system. The encryption-controlling application is also identified on all infected systems. Users can then use “One-Click Kill” to eradicate the detected ransomware throughout the organization with just a single mouse click.
Sangfor Endpoint Secure also integrates with Sangfor’s entire range of security solutions, including Sangfor NGAF, Sangfor IAG, and Sangfor Cyber Command as part of Sangfor’s XDDR solution. With data collection and correlation at the perimeter, endpoint, and network, Sangfor XDDR is a holistic threat detection and response solution that provides organizations with ultimate protection against the most sophisticated of threats like ransomware and advanced persistent threats (APT).
Sangfor's Endpoint Secure has garnered significant success and helped many organizations improve their security.
- J&T Express, a logistics company with the largest shipping volume in Indonesia, has achieved maximum safety and efficiency by utilizing a combination of Sangfor’s security solutions – Cyber Command, Next Generation Application Firewall, Endpoint Secure, and Internet Access Gateway.
- Mitra Keluarga Hospital is a leading community hospital operator in Indonesia with high profitability and success rates. It made use of Sangfor solutions of Next Generation Firewall, Sangfor Endpoint Secure, and Internet Access Gateway (IAG) to strengthen its data security and malware protection.
- Mahasarakham University (MSU) is the second higher education institution and the fourth university in the Northeast region of Thailand. MSU deployed Sangfor's Endpoint Detection and Response to work together with the other solutions within the organization to enhance protection and facilitate centralized management.
Watch the video to learn how Sangfor Endpoint Secure shows its best of the best capability to detect process injection.
Frequently Asked Questions
Contrary to what most business owners believe, small to medium sized businesses actually get attacked more often than large corporations. Between 2020 and 2021, corporate networks saw 50% more cyber attacks per week and 40% of small businesses that faced a severe attack experienced at least eight hours of downtime. 43% of all cyber attacks are aimed at small businesses, but only 14% have the right tools to defend themselves. 61% of small to medium sized businesses have reported at least one cyber attack during their previous calendar year, and these numbers continue to grow annually.
Most small businesses that are unwilling to invest in their own cyber security end up paying more to remedies and ransoms than what a security solution would have cost. Having professional-grade EDR tools and a cyber security solution in place significantly reduces your risks and saves you all the headaches in the aftermath of an attack.
EDR and NDR tools, like other cyber security solutions, are not mutually exclusive but can complement each other and form a formidable defense together. Unless you are spending on tools that have similar or overlapping functions, most businesses and organizations would benefit from having more tools and a more holistic solution than otherwise.
EDR tools are extremely effective in dealing with malicious files discovered at endpoints, but they are by no means a complete cyber security solution and should ideally be used in conjunction with other tools.
For small and medium-size businesses looking for a holistic cyber security solution, Sangfor’s NGAF (next generation firewall) is an excellent choice. Its simplified GUI dashboard offers easy management and monitoring even for smaller IT security teams and can eliminate up to 99% of malware at the perimeter. It also integrates with Sangfor Endpoint Secure to respond together to malware discovered on endpoints, effectively mitigating most cyber threats that most businesses face regularly.
As malware and threats continue to develop and evolve at a rapid pace, the difficulty in containing them also increases exponentially every day. Dealing with newer and more advanced malware requires the newest technology and security features, which most free EDR tools often cannot provide. Sangfor Endpoint Secure, for example, offers exceptional threat detection and response capabilities. Very few professional-grade EDR tools or cyber security solutions can match the level of protection provided by its features, and it’s unlikely that you can find them in free tools.





