Definition of NDR - Network Detection and Response
NDR is a type of network security solution that monitors and analyzes all network traffic, including north/south and east/west traffic, using strategically placed sensors. When suspicious traffic patterns are detected, NDR responds automatically to the threat or sends alerts to security operators for further investigation. Threat correlation is a key feature of NDR and provides security teams with the context to simplify forensic investigation, threat hunting, and risk remediation. Gartner Inc. defines network detection and response (NDR) as using “non-signature-based techniques (for example, machine learning or other analytical techniques) to detect suspicious traffic on enterprise networks. NDR tools continuously analyze raw traffic and/or flow records to build models that reflect normal network behavior.”
Why Choose NDR - Network Detection and Response?
Organizations are facing an increasingly dangerous threat landscape. On the one hand, threat actors are constantly refining and developing new tactics, techniques, and procedures (TTPs) to evade security detection and cause more damage. On the other hand, accelerated digital transformation in the past few years has widened organizations’ attack surface, presenting adversaries with more weaknesses to exploit. The number of global security incidents has increased by a staggering 75% over the past 5 years, with small and medium-sized businesses (SMBs) targeted 61% of the time. While taking down large enterprises with deep pockets is the ultimate goal, attackers have found it far easier to attack smaller businesses with less robust cybersecurity capabilities. They then use the data and access they steal to climb the ladder and attack larger partner enterprises or even attack customers directly. Ransomware continues to be the fastest-growing type of cybercrime, with profits reaching $265 billion annually by 2031.
When enhancing your network security capabilities, remember that no individual security solution offers 100% protection. This must be a collaborative effort between multiple security solutions and qualified security personnel. Recognized as one of the pillars of the Gartner SOC Visibility Triad, network detection and response is fast becoming a must-have component in a security operation center (SOC) to help security teams detect the most advanced threats.

What Type of Threats Can NDR Solutions Uncover?
NDR solutions cover several types of cybersecurity risks. They include:
- Malware and Intrusions: NDR can identify the presence of malware and unauthorized intrusions by analyzing network traffic and behavior, and detecting suspicious activities and known malicious indicators.
- Insider Threats: NDR monitors user behavior and access patterns to detect insider threats, such as unauthorized access attempts, unusual activities, or data exfiltration attempts by employees or authorized users with malicious intent.
- Data Loss and Leakage: NDR detects data loss and leakage incidents by monitoring data transfers, identifying abnormal data flows, and detecting unauthorized data access attempts.
- Advanced Persistent Threats (APTs): NDRs analyze network behavior to uncover signs of sophisticated and targeted attacks, such as command-and-control communications, lateral movement, and privilege escalation attempts associated with advanced persistent threats.
How NDR Works in Threat Detection and Response
Network Detection and Response (NDR) assumes that threats already exist within the network and takes a proactive approach to identifying and mitigating them.
Here’s how it works:
- Monitors and analyzes traffic from across the network to provide security teams with complete visibility of network activity and network devices.
- Uses machine learning to develop baselines for normal network behavior and continuously applies AI traffic analysis to detect activity that does not comply.
- Detects threats in real-time and coordinates with other security tools to respond automatically to detected threats or provides timely alerts for incident response teams.
- Correlates traffic from various data sources to determine how threats entered and moved through the network to streamline incident response and threat-hunting efforts.
Let’s drill down even deeper into how NDR works in terms of monitoring, detection, and response.
Providing Complete Network Visibility
NDR addresses blind spots by continuously monitoring network traffic and discovering every connected device, including unknown or shadow assets. This gives security teams the visibility they need to detect threats and ensure no device is left exposed.
Detecting Irregular Behavior to Uncovering Threats
Modern attacks often avoid detection by using legitimate tools in unexpected ways. NDR overcomes this by using machine learning to define “normal” behavior and spot deviations. It aggregates and correlates traffic data, using AI and behavioral analytics to detect hidden threats like fileless malware, often missed by signature-based tools.
Initiating Automated and Coordinated Response
When threats are detected, NDR can automatically trigger responses through orchestration with other security tools. For instance, it can:
- Block malicious communication at the firewall level
- Isolate compromised hosts
- Trigger endpoint scans
- Alert security teams for manual investigation
This real-time, coordinated approach helps contain threats quickly, before they escalate. It could also instruct the endpoint detection and response (EDR) solution to run a self-scan and wipe any malicious files. Alternatively, security teams can be alerted for manual investigation and response.
Advantages of Network Detection and Response
By now, you should have a pretty clear idea of how NDR works and its superior threat detection and response capabilities. Let’s now go through a few key advantages NDR provides.
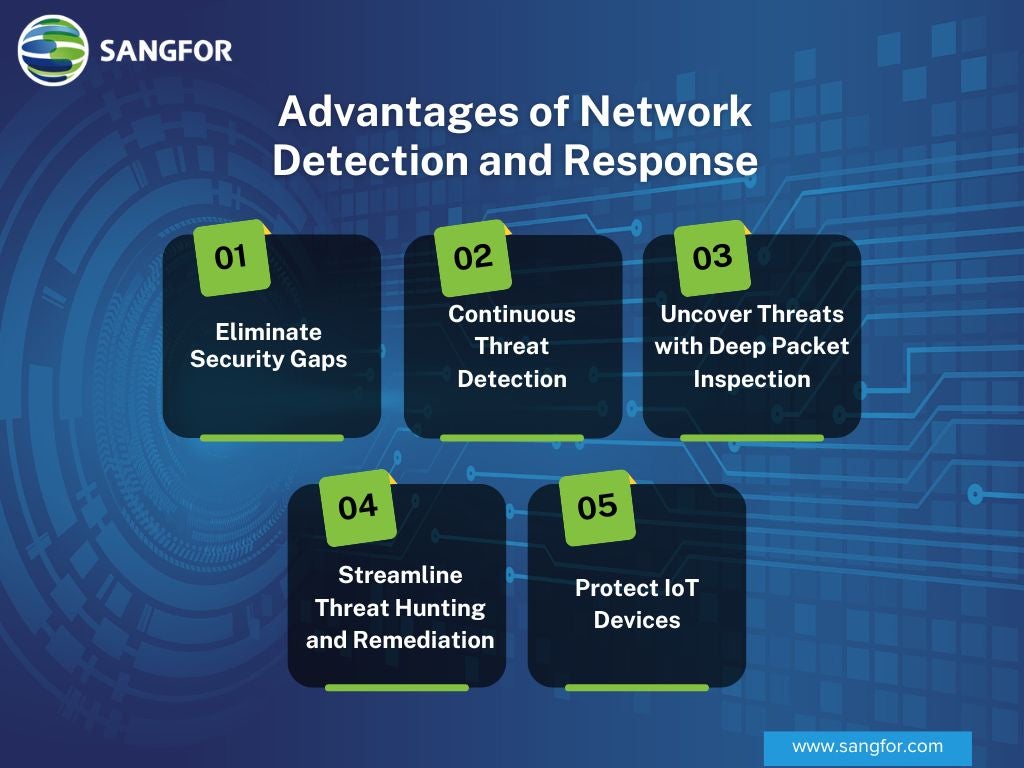
Eliminate Security Gaps
Point solutions like firewalls and EDR generally do a decent job at their respective functions, but gaps exist between each solution’s sphere of influence that allow threats to evade detection. Network detection and response is the last piece of the jigsaw that plugs these gaps. By monitoring and analyzing traffic across the entire network, NDR creates a foolproof system against which no threat can hide. You should remember that attacks that are the most difficult to detect tend to be the most devastating. That is why keeping out the last 1% of the most dangerous threats prevents catastrophic losses and impact, and could be the difference between life and death for small and mid-size businesses.
Continuous Threat Detection
One weakness of the majority of security tools is that they can be evaded or even disabled. For example, attackers can bypass firewall rules using various evasion techniques, such as spoofing the IP address and using a proxy server. Attackers can also kill the processes that endpoint security tools like antivirus and EDR rely on to run. The advantage of threat detection at the network layer is that cyberattacks generate traffic one way or another, so they cannot hide their activity. NDR solutions cannot be switched off either, due to the way they are designed. In fact, attackers won’t even know that their activities are being monitored by NDR and will be less careful. While other security tools can fail, NDR provides a continuous and robust last line of defense.
Uncover Threats with Deep Packet Inspection
It is estimated that over 90% of malware is hidden in encrypted traffic. Only with deep packet inspection could security tools uncover this kind of malicious code. This is indeed possible with firewalls and EDR solutions. However, they typically do so in a way that consumes too many computing resources. Network detection and response solutions, on the other hand, use out-of-band decryption, which does not cause performance degradation. Therefore, NDR provides the visibility needed to detect threats in encrypted traffic without affecting performance.
Streamline Threat Hunting and Remediation
Correlating traffic from across the network not only enables NDR to detect anomalous activity to uncover threats but also streamlines forensic investigation after the security incident. By being able to chain the malicious activities together, security analysts can trace the attack step-by-step back to the point of entry and find out the root cause of the attack. This is critical for threat hunting to remove any residual threats and remediate any weaknesses that enabled the threat to penetrate and spread through the network, thus preventing future exploitation of the same weaknesses.
Protect IoT Devices
IoT, short for the Internet of Things, is a category of devices that can connect to the Internet other than conventional devices like PCs, laptops, and mobile phones. IoT devices such as smart light bulbs, thermostats, and printers are gaining popularity in offices. Industrial and medical IoT devices are also being widely adopted. The problem with IoT devices is that most contain vulnerabilities and don’t have the computing resources to be installed with endpoint security software. As a result, IoT devices are increasingly being exploited by threat actors to gain network access. NDR is equipped to protect IoT devices in two ways: first, to detect their presence on the network (IoT devices are often not reported to IT and become shadow assets), and second, to detect anomalous behavior to and from IoT devices.
Shortcomings of NDR Solutions
While NDR solutions provide many distinct advantages, they have several shortcomings that organizations should be aware of. These include:
- Blind Spots: NDR solutions can have blind spots when it comes to encrypted traffic, making it difficult to detect threats within encrypted communications.
- False Positives and Negatives: NDR solutions may generate false positives, flagging legitimate activities as threats, which can lead to wasted time and resources. Conversely, false negatives can occur when NDRs fail to detect actual threats, leaving organizations vulnerable to attacks.
- Limited Endpoint Visibility: NDR solutions primarily focus on network monitoring and may have limited visibility into endpoints, such as individual devices or user activities. This can hinder the detection of threats originating from endpoints and impede comprehensive threat analysis.
- Complexity and Resource Requirements: Implementing and managing NDR solutions can be complex, requiring specialized skills and resources. Organizations need to ensure they have the necessary expertise and infrastructure to deploy and maintain these solutions effectively.
Organizations should carefully consider these limitations and assess how they align with their specific cybersecurity requirements before implementing an NDR solution. It is crucial to complement NDR with other security measures to build a well-rounded and robust cybersecurity defense.
Key Considerations for Choosing the Right NDR Solution
When selecting an NDR solution, several factors should be considered to ensure the right fit for your organization's cybersecurity needs. Here are key points to consider:
- Coverage and Visibility: Evaluate the solution's ability to provide comprehensive coverage and visibility across your network infrastructure, including physical, virtual, and cloud environments. Ensure it can monitor network traffic, endpoints, and encrypted communications effectively. Look for an NDR solution that provides network-wide visibility, allowing IT teams to analyze and monitor threats with more accuracy. This visibility helps reduce false positive alerts and ensures faster detection and response to malware.
- Threat Detection Capabilities: Assess the solution's detection capabilities for a wide range of threats, including malware, intrusions, insider threats, data loss, and advanced persistent threats (APTs). Look for features like behavioral analytics, machine learning, and threat intelligence integration to enhance detection accuracy.
- Scalability and Performance: Consider the scalability of the solution to accommodate your network's size and growth. Verify its performance capabilities to handle high network traffic volumes without impacting network performance or causing latency issues.
- Integration and Compatibility: Determine how well the NDR solution integrates with your existing security infrastructure and tools. Compatibility with your network architecture, security information, and event management (SIEM) system, and other security solutions can streamline operations and enhance threat response. As many industries adopt a cloud-first approach, ensure the NDR solution is cloud-ready and can work in multi-cloud environments.
- Usability and Reporting: Evaluate the user interface and ease of use of the NDR solution. Look for intuitive dashboards, customizable reports, and alerting mechanisms that provide actionable insights and facilitate efficient incident response.
- Compliance and Regulatory Support: Ensure the NDR solution aligns with industry regulations and compliance requirements relevant to your organization. Look for features that support compliance reporting, log retention, and data privacy.
- Vendor Reputation and Support: Research the vendor's reputation, expertise, and customer reviews. Consider their track record in delivering reliable and timely support, including software updates, patches, and access to knowledgeable technical support.
By considering these points, you can make an informed decision when selecting an NDR solution that effectively addresses your organization's cybersecurity needs and aligns with your long-term security strategy.
Sangfor’s Intelligent NDR Solution
Sangfor Technologies has been a leader in threat detection and response solutions for many years. We developed our Cyber Command NDR solution to push the boundaries of threat detection and response using our XDDR security framework. XDDR integrates NDR with all of Sangfor's and certain third-party security products to deliver a holistic way to combat ransomware and APTs that use weaponized AI. Cyber Command uses AI models designed for specific threat-hunting use cases to detect and remove weaponized AI.
Sangfor recognized the need for an artificially intelligent network detection and response system to counter the ever-growing list of cyber threats. That’s why Sangfor’s R&D team developed the Sangfor Cyber Command. Cyber Command features sophisticated detection capabilities thanks to the broad range of intelligent technologies, such as machine learning and AI analysis. The Cyber Command Response Center allows administrators to watch the network carefully, with contextualized and easy-to-read logs ready at the touch of a button. Combined with Sangfor Endpoint Secure and Sangfor Network Secure - Next Generation Firewall, Cyber Command delivers rapid response for maximum security and protection of your network.
Typically, firewalls are designed to only monitor the traffic that goes through the firewall itself. Sangfor Cyber Command does something called Network Traffic Analysis (NTA). We sit right next to one of your core switches and analyze all your traffic.
Jason Yuan, VP of Sangfor International Market
Sangfor Cyber Command “What is NDR” Whiteboard Video
Sangfor’s security team made a whiteboard video to explain the ins and outs of Network Detection and Response. In this video, Jason Yuan provides a simple yet informative explanation of NDR and Sangfor’s NDR solution, Cyber Command.
Sangfor NDR Success Stories
- The Azienda Socio Sanitaria Territoriale (ASST) Lariana is an established healthcare provider in the Province of Como, Italy. Sangfor Cyber Command gave the healthcare providers 360-degree visibility of the network to ensure cybersecurity.
- Naquadria S.r.l. is a reliable internet service provider and data center based in Piacenza, Italy. Sangfor’s Cyber Command NDR (Network Detection and Response) solution provided Naquadria with a reliable and advanced control and response center for all threats that plagued the exposed systems, including the web and mail servers.
The Future of NDR
The global Network Detection and Response (NDR) market is set to grow at a CAGR of 17.5% by 2026, highlighting its importance as a leading network security solution. With the rise of sophisticated ransomware and malware, robust security measures are essential.
Sangfor Technologies leverages advanced machine learning and AI to enhance its network security and cloud solutions. Our flagship product, Sangfor Cyber Command, uses AI-driven threat detection and response, ensuring your network’s safety. This technology helps organizations quickly identify and mitigate security incidents, reducing potential damage and downtime. Beyond NDR, Sangfor’s solutions include AI-powered secure cloud services and endpoint protection, designed to simplify IT management and enhance security. For more information on how Sangfor can support your cybersecurity needs, contact us today.
Contact Us for Business Inquiry
Frequently Asked Questions
Network detection and response (NDR) is a cybersecurity solution used to detect and respond to cyberattacks that have already breached a computer network. These are likely to be advanced cyberattacks that were missed by other security solutions and have the potential to cause a major impact.
In terms of threat detection, the basic concept of NDR is to detect irregular behavior in network traffic. Because malicious activity is different from normal network activity, a cyber-attack will show up as irregular behavior in network traffic. To detect irregular behavior, NDR uses machine learning to learn what is considered normal behavior over time. Traffic from across the network is continuously analyzed to detect any activities that deviate from normal behavior.
Because the primary function of NDR is advanced threat detection, it is most needed by organizations that are often targeted by sophisticated cyberattacks. These include medium to large enterprises, government agencies, and critical public infrastructure such as energy and communication infrastructure, hospitals, schools and universities. Managed service providers (MSPs) that have access to the networks of large enterprise customers and government agencies are often targeted by sophisticated supply chain attacks.
NDR is different from other cybersecurity solutions in various aspects. The main differences are:
- Sphere of influence: Most cybersecurity solutions are point solutions, that is, they can only protect a particular space. For example, firewalls only protect the network perimeter, controlling what enters and exits the network. Endpoint security software, such as antivirus, only protects the device it is installed on. NDR takes a holistic approach to threat detection by taking into account all network traffic.
- Method of threat detection: Most traditional cybersecurity solutions rely on signature-based detection, that is, the detection of malware based on known features and patterns. NDR uses anomaly-based detection, that is, the detection of malware and cyber-attacks based on irregular activity. Anomaly-based detection is more accurate for detecting unknown malware and new tactics and techniques used by attackers.
Using cybersecurity solutions such as a firewall and endpoint security software is not only standard practice but also enhances the effectiveness of NDR. In terms of threat detection, NDR can correlate traffic and logs from other security solutions to make better sense of network activity. This helps to produce more accurate threat detection rates. In terms of threat response, NDR can be configured to respond to detected threats by coordinating with other security solutions, for example, to ask the firewall to block a specific IP address.
By taking a holistic approach to threat detection, NDR is equipped to detect advanced cyberattacks missed by point solutions. These attacks are the most dangerous and have the potential to cause major damage, such as the theft of sensitive data and encryption by ransomware. By being able to detect these attacks, NDR ultimately helps organizations minimize or avoid data and financial losses, ensure business continuity, and protect their reputation.
Sangfor provides NDR as part of its Cyber Guardian managed detection and response (MDR) service. In this service, Sangfor deploys its Cyber Command NDR solution in your environment, and its security experts monitor your network traffic 24/7 to detect and respond to signs of cyber-attack. Essentially, Sangfor provides the technology and personnel so that customers can enjoy professional security protection without capital investment.
