Today everything is connected through the internet – billions of pieces of data are constantly being transferred to and from our phones, laptops, smartwatches, and every other device connected to a network. This unsurmountable surge of data traverses through cyberspace by breaking up into smaller “data packets” for the sake of transmission, then reassembles itself at its destination. This data movement causes the phenomena of network traffic.
What Is Network Traffic?
Network traffic is the traveling of data through a network. Different activities and behavior will result in different types of network traffic activity. There are different categories into which these traffic levels can be placed:
- Heavy traffic where high amounts of bandwidth are utilized - these would be extremely active and constant network traffic routes.
- Interactive traffic where bandwidth prioritization takes place - resulting in slower responses without web and application traffic limitations in place.
- Non-real-time traffic refers to bandwidth consumption mainly during public working hours – such as HTTP, FTP, and e-mail.
- Latency-sensitive traffic risks slower data retrieval as the ability of data transfer across the network is cut down drastically.
The 7 OSI Model Layers
In order to properly visualize the process of network traffic, it is described using the OSI Model (Open Systems Interconnection Model) - an abstract conceptualization of the 7 layers of network communication published in 1984 by the International Organization for Standardization (ISO).
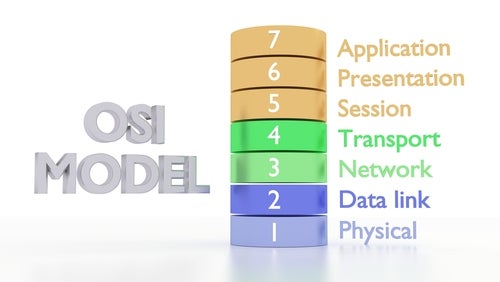
The framework goes as follows:
- Physical Layer: The first and lowest layer is concerning the physical and electrical link between networks. This can range from electric circuits and cables to voltages and Wi-Fi signals – anything which acts as the immediate interface for the transmission of raw data.
- Data Link Layer: The data link layer functions mainly to detect and correct errors made in the physical layer and to pack data bytes into frames to transmit to the network layer and packet synchronization. This layer is usually divided into the subcategories of Media Access Control (MAC) and Logical Link Control (LLC) as well.
- Network Layer: The third layer of the model is responsible for the routing of data packets from the source to the destination host through one or more networks. The network layer issues service requirements of the data link layer and responds to service requests from the transport layer.
- Transport Layer: The transport layer manages connections and errors in order to deliver data to the appropriate application process of the host computer. The most well-known transport protocol of this layer is the Transmission Control Protocol (TCP).
- Session Layer: This layer facilitates a dialogue between the two devices trying to communicate information. Session layer services are mostly used in application settings that make use of remote procedure calls (RPCs) and provide checkpointing, adjournment, termination and restart procedures.
- Presentation Layer: The presentation layer ensures that data relayed to the application layer is easy to read and accessible. Decryption and encryption happen mostly here – making this layer necessary for the conversion of data into a more “presentable” transmission.
- Application Layer: The final layer of the networking model is the one closest to the user output – giving users a direct interface and form of access to the network at this layer. Services that rely on the application layer include TelNet, FTP, and everyday web browsers.
Once you can properly understand and envisage the network traffic layers that your data needs to travel through in order to reach its destination, you can see the relevance of a detailed network traffic analysis tool to monitor and secure that line of transmission.
What Is Network Traffic Analysis - NTA?

Network traffic analysis (NTA) is an advanced method for the inspection and breakdown of the data packets that form network traffic by use of a combination of behavior modeling, machine learning, and rule-based detection to root out any suspicious activity. A baseline of normal behavior can be identified through this analysis and any outliers can be flagged down and isolated as potential threats.
While this is mostly used for security purposes, network traffic analysis can also be used for capacity planning and identifying surges of network traffic in certain areas.
This rapid communication of data presents several vulnerabilities for your company - which leans into why exactly tools for network traffic analysis solution are necessary.
Why do you need an NTA - Network Traffic Analysis Solution?
Drastic strides in technology have made sure that most companies and people rely heavily on online networks and the constant availability of data. Business dealings have become much easier with the world at our fingertips. Still, the data we depend on is always vulnerable to cyber-attacks – especially sensitive data that could cripple production and tarnish the reputation of a company.
Therefore, numerous reasons exist to invest in elite network traffic analysis tools:
- Increased interest in corporate data: The rise in ransomware and malware attacks has pushed criminals to target business servers in the hopes of receiving higher ransoms for the decryption of client-sensitive data. Network analysis would help curb this trend by providing automatic anomaly detection and preventing breaches before they happen.
- Stronger Network Performance: Network traffic analysis allows companies to assess where network traffic might spike and will enable them to adapt and improve efficiency to avoid bottlenecks. This also helps with effective resource management – cutting down on IT costs.
- Advanced Public Security Stature: A company using effective network traffic analysis tools presents itself to the public as more reliable and determined to provide more efficient services – this attracts potential clients and deters potential hackers who may try to infiltrate your business.
- Resource Efficiency: The constant active monitoring of network traffic is impractical for most company staff to maintain. The automation of this process gives businesses a consistent level of advanced analysis while cutting the cost of workers and overhead expenditure.
- Rapid Response: Finding threats quickly leads to less damage to the server. With an advanced network traffic analysis tool, the time taken to discover and mitigate these risks is dramatically shorter - ensuring minimal damage is taken.
Once it has been established that your company does in fact need a superior network traffic analysis tool in place, it becomes a question of what exactly to look out for when trying to find one that is best suited to your needs.
What Are the Key Features of a Network Traffic Analysis Tool?
Here is a round-up of some of the most pertinent features that an improved network traffic analysis tool should have in order to effectively protect you and your business:
- A user-friendly interface: Network traffic analysis requires large quantities of complex data to be processed and it would benefit you if the solution hosted a simplified Graphical User Interface (GUI) for ease of operation and the ability to visualize and navigate information easily.
- Built-in Threat Intelligence: A superior network traffic analysis tool features elaborate and advanced self-learning technology to track and hunt down suspicious files before they have the chance to infect or exfiltrate data. Making use of Artificial Intelligence and machine learning technology helps the tool to effectively process and inspect data proficiently.
- Integration: The ability to provide comprehensive protection of the network by integrating data from numerous sources. Integration also helps third-party IT systems, such as Security Information and Event Management (SIEM) or Security Operations Center (SOC). Integrations can be enabled through Application Programming Interfaces (APIs), pre-built connectors, or open-sourced architectures and allow for a closed-loop process.
- Coverage of key metrics: Network traffic analysis should be able to observe and critically analyze data within a wide system of measurements – such as bandwidth utilization per application, time-bound trends, and traffic flow.
- Accessibility: A comprehensive network traffic analysis tool caters to the client and offers a simplified dashboard for better visualization and monitoring of data trends and behavioral patterns.
- Actionable Insights: The simple detection of potential threats is an essential aspect of network traffic analysis tools, but not at all the extent to which they can function. The response from the solution chosen should give clear directives about mitigating the problem and offer tangible solutions on how to optimize bandwidth, secure networks and provide intricate pattern analysis for future data security.
- Cloud Comprehension: The ability to monitor cloud traffic is a key feature in network traffic analysis. With a significant proportion of networking activity taking place in the cloud – understanding cloud computing becomes a pivotal point for a viable network traffic analysis tool. To provide true end-to-end visibility, your company should be able to navigate virtual private cloud infrastructure, cloud monitoring logs, and Application Programming Interfaces (API).
This might all seem like a tall ask for a single cyber security solution to cover but Sangfor has the perfect comprehensive answer to your network traffic analysis needs with the exceptional and advanced Cyber Command NDR Platform.
Sangfor’s Cyber Command NDR Platform
Gartner says, “Applying machine learning and other analytical techniques to network traffic are helping enterprises detect suspicious traffic that other security tools are missing”. That’s where Cyber Command comes in – a threat hunting tool to make network security traffic analysis simple.
Cyber Command improves security detection and response capabilities by monitoring internal network traffic and integrating network and endpoint security solutions for automated responses. This also entails uncovering breaches of existing security controls while impact analysis identifies hidden threats within the network.
By applying AI technology and Sangfor’s singular “Golden Eye” behavior analysis feature, Cyber Command can study patterns and strengthen external and internal system defenses. Aided by global threat intelligence, Cyber Command simplifies cyber forensics by providing complete visibility of the threat kill chain – allowing for better navigation and understanding of network traffic trends and threats.
Watch this introduction to Sangfor Cyber Command NDR Platform and the ways it serves to secure your company and provides advanced network traffic analysis for your network.
Introducing: Cyber Command - Threat Detection and Response Platform
The integration with Sangfor’s Endpoint Secure and Next Generation Firewall NGFW offers a fully comprehensive security, analysis, and monitoring solution for your company. Additionally, the superior cloud computing technology ensures that Sangfor offers data security especially suited to the cloud.
Check the success stories of our satisfied clients who have used Cyber Command in their organizations that bear testament to the comprehensive and secure network traffic analysis tools that Sangfor’s Cyber Command NDR Platform afforded them:
- The Azienda Socio Sanitaria Territoriale (ASST) Lariana is an established healthcare provider in the Province of Como, Italy. Sangfor Cyber Command gave the healthcare providers 360-degree visibility of the network to ensure cybersecurity.
- Naquadria S.r.l. is a reliable internet service provider and data center based in Piacenza, Italy. Sangfor’s Cyber Command NDR (Network Detection and Response) solution provided Naquadria with a reliable and advanced control and response center for all threats that plagued the exposed systems - including the web and mail servers.
Watch this whiteboard video presented by Jason Yuan, Sangfor’s VP for Product & Marketing, to learn more about Sangfor’s Cyber Command NDR Platform.
Whiteboard Story: What is NDR? | Sangfor Cyber Command
For more information on Sangfor’s cyber security and cloud computing solutions, visit www.sangfor.com.





