Cyber-attacks are now increasing in volume and complexity. This has made threat-hunting tools an essential part of any modern organization’s cybersecurity strategy. Threat actors often lurk in networks for weeks or even months before they are discovered, posing a significant risk to data, information, and services.
However, not all organizations can afford threat-hunting tools or even know where to start when it comes to cyber threat hunting. Fortunately, modern threat-hunting tools have made it easier for companies to deploy established cyber threat-hunting systems – ensuring an extra layer of protection for your network.

What Is Cyber Threat Hunting?
Threat hunting - or cyber threat hunting - is the process of proactively analyzing an organization’s network to identify threats and eliminate them. By doing so, companies have a better understanding of their cybersecurity posture and how to improve it.
Cyber threat-hunting tools use information gathered by security analysts and threat intelligence to form different threat-hunting techniques. These cyber threat-hunting tools also make use of user & entity behavior analytics, and endpoint detection and response (EDR) to monitor and defend the network and operating systems, employing the tactics, techniques, and procedures (TTPs) used by cybercriminals to evade detection.
The threat-hunting methodology consists of 3 elements: an initial trigger phase, an investigation phase, and a resolution phase.
- Trigger Phase - This is typically the starting point. In the threat-hunting process, the threat hunter will collect information and formulate an idea of a potential attack. It then chooses a trigger for when that attack is forming.
- Investigation Phase - Once a trigger has been created, the threat hunter looks at the anomalies present that either confirm or refute the threat hypothesis.
- Resolution Phase - After gathering enough information on the potential threats, the hunter gives the data to the cybersecurity team and other threat detection tools for evaluation, prioritization, analysis, and storage.
These come together to form a stable threat-hunting platform to secure your network and data from a cyber-attack.

What Are Threat Hunting Tools?
Threat hunting tools are essential resources used during a threat hunt. They encompass various software and equipment that allow cybersecurity professionals to find and handle threats in a network.
These tools have a wide range of services - including analytical insights, security monitoring, integrated security information, automation, response systems, and managed detection and response systems. In the ever-evolving threat landscape, these tools help enhance the security posture of organizations by streamlining the identification of threats.
In the past, threat hunting could have taken a significant amount of time to complete. This is because the data, intelligence, logs, history, and research would have to be done manually. However, these threat-hunting tools now allow threat hunters to quickly and efficiently find threats to streamline the entire threat-hunting process.
Types of Threat Hunting Tools and Platforms
Threat-hunting platforms use different tools to fully analyze and detect threats within the system. These are all specific in function and play vital roles in seeking out suspicious or anomalous behavior. Broadly, they are categorized into five sets of threat-hunting tools:
- Free SIEM Tools: These are the usual Security information and event management (SIEM) solutions available that provide real-time threat analysis and raw security data management capabilities. They help investigate anomalies, identify root causes, and react swiftly, which is crucial for modern security teams in security operations centers (SOCs), streamlining threat detection and incident response through the application of AI and ML technologies.
- Security Monitoring Tools: These tools collect and monitor threats to your network’s cybersecurity through antivirus agents, firewalls, and endpoint security measures, consolidating and analyzing security logs from various sources. Endpoint security monitoring tools offer host-level security visibility. With continuous monitoring of the events and activities in real-time, these tools aid in swift threat detection and response.
- Analytics Tools: Using statistical knowledge, behavior analytics and machine learning, these tools provide clear and concise patterns created by network usage through scores, charts or reports to help cybersecurity personnel find any potential threats.
- SOAR Systems: Security Orchestration, Automation, and Response (SOAR) systems apply a better level of protection through automated management and effective identification of threats.
- MDR Systems: These Managed Detection and Response (MDR) systems are a third-party security layer that constantly monitors the network for threats.These systems leverage advanced analytic technology and provide crucial data to enable precise threat detection and quickly repair compromised endpoints.
- AI-driven analytics:Many tools now incorporate AI-driven analytics, enhancing their ability to detect patterns and anomalies more effectively. This means threat-hunting tools can learn from previous incidents and adapt their strategies, making them invaluable assets in an ever-evolving threat landscape.
These cyber threat-hunting tools should be optimized with machine learning and AI technology to provide automated and advanced protection. They can also be integrated to form a stable and reinforced shield against threats.
With the sheer volume of data flowing through a company daily, automation is vital to the threat-hunting process. Businesses of all sizes should invest in managed threat-hunting tools and automated threat-hunting platforms that are designed to consistently perform all these necessary functions.
Why Do You Need Threat Hunting Tools?
The need for threat hunting arises from the limitations of these traditional cybersecurity measures. Attackers can navigate through networks and steal data if they cross boundaries undetected. Proactive threat hunting identifies and patches vulnerabilities before exploitation occurs, limiting the duration of successful attacks and their damage.
Proactive threat hunting attempts to identify and patch vulnerabilities before they are exploited by cybercriminals, thereby reducing the number of successful breaches. It also meticulously analyzes all data generated by applications, systems, devices, and users to identify anomalies that indicate a breach is occurring, thus limiting the duration of successful attacks and the damage caused. Furthermore, cyber threat hunting techniques often involve unifying security monitoring, detection, and response through a centralized platform, offering greater visibility and increasing efficiency.
Advantages of Threat Hunting Tools
Organizations leveraging threat hunting tools can benefit from:
- Proactive Vulnerability Detection: Threat hunting tools prioritize proactive security measures, such as scanning the network for unpatched software, misconfigurations, and other potential entry points that could be used by cybercriminals, to prevent attackers from leveraging weaknesses in the system. This preemptive approach significantly strengthens an organization’s defense against cyber threats.
- Enhanced Efficiency in Threat Response: Businesses striving for streamlined cybersecurity operations will see the value in threat hunting tools. Through the automation of security tasks, these tools enable businesses to facilitate response strategies faster and more effectively, optimizing the use of resources. Tools that are integrated with Security Information and Event Management (SIEM) solutions can run real-time threat analysis and swift threat detection, elevating the efficiency of cybersecurity to a new height.
- Holistic Visibility into Cybersecurity Operations: Organizations desiring a thorough overview of their network's security will benefit from the visibility and transparency offered by threat hunting tools. These tools aggregate and correlate data from various sources, such as logs, network devices, and endpoints, to construct a comprehensive view of the network's security landscape. This allows the organizations to identify the areas in the network’s architecture and security protocols that require improvements.
- Minimizing the Impact of Breaches: For entities aiming to minimize the consequences of security incidents, threat hunting tools curtail the period attackers can operate undetected within a network and diminish the extent of damage inflicted, protecting sensitive information and ensuring operational continuity.
Disadvantages of Threat Hunting Tools
While threat hunting tools can bring numerous advantages across sectors and industries, they present several challenges that businesses and organizations may come across when using them:
- Need for Specialized Personnel: To utilize threat hunting tools effectively requires the organization to have trained personnel with specialized skills in network security, system monitoring. It is also important that they possess knowledge in identifying attacker behavior patterns and tactics. Furthermore, skilled professionals are needed to configure and maintain the tools, and analyze the collected data. Acquiring such experts can be a challenge for any business.
- Possible False Positives: Threat hunting tools mostly rely on complex algorithms and behavioral analysis to detect potential threats. While these tools aim to minimize false positives, there is still a possibility of generating false alarms. False alarms can squander resources and redirect the focus of cybersecurity professionals away from legitimate threats. Organizations must invest time and effort in fine-tuning the technologies to limit the number of false positives.
- Time-Consuming Maintenance and Updates: Cybersecurity professionals and teams need to dedicate and allocate a significant amount of time to update and maintain the tools, so they can stay effective against the constantly evolving threats. These regular maintenance routines may include software updates, patching vulnerabilities and keeping up with the latest threat intelligence. Failure to keep the tools up to date may render them less effective in detecting emerging threats.
- High Resource Requirements: Using and putting threat hunting technologies into practice needs a lot of resources. A significant quantity of data is produced by these tools, and it must be gathered, saved, and examined. To handle the volume of data, organizations need to make sure they have enough processing power and storage capacity. The tools could also need specialized software or hardware infrastructure, which would add to the expense.
Things to Consider When Choosing a Threat Hunting Tool
When it comes to the stage of you finally needing to decide on a threat hunting tool for your business or organization, it is imperative to consider tools that are equipped with the right features for your solution. The following are some of the most important factors that every organization needs to consider before selection:
- Flexibility and Scalability: Consider a threat hunting tool that offers flexibility to adapt to your organization's changing needs. Look for a tool that can accommodate different architectures, hardware, applications and locations. This ensures that you can scale your operations up or down as necessary.
- Data Source Monitoring: A threat hunting tool should be able to monitor multiple data sources, including internal and third-party systems. This should offer the cybersecurity team or personnel more holistic information regarding the network status and a comprehensive view of potential threats.
- User-Friendly Interface: A user-friendly interface reduces the learning curve and enables your team to quickly leverage the tool's capabilities without missing critical information. This is particularly important even for skilled teams who have undergone training.
- Actionable Reporting: Ensure that the tool provides intuitive reporting capabilities. Your team should receive clear and concise information on whether action is required and what steps to take. Actionable reporting enables efficient decision-making and response to potential threats.
- Seamless Integrations: The right tool should integrate with various sources and solutions. This allows you to customize and optimize your threat hunting ecosystem by connecting with internal and external systems effectively.
Best Free Open-Source Threat Hunting Tools
Most smaller companies rely on open-source threat-hunting software. This is because it can be more affordable and accessible for their businesses. While these threat-hunting solutions are usually freely available online, choosing the correct one can be slightly tricky at times.
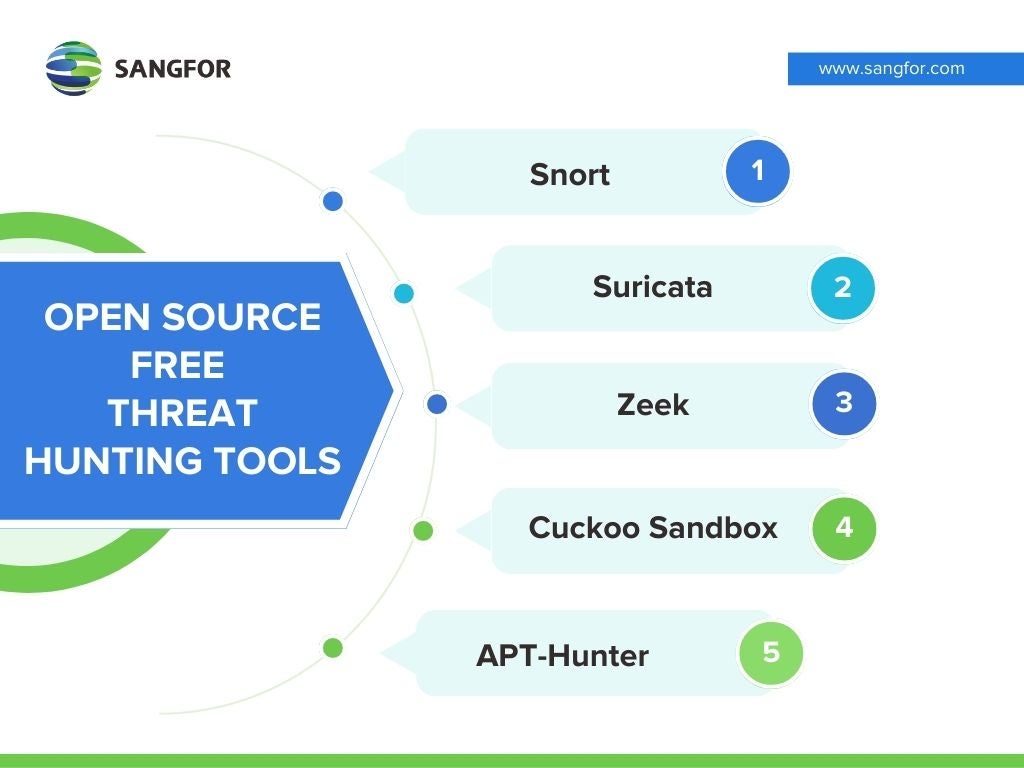
Some of the best threat-hunting tools we’ve rounded up that are freely available include:
1. Snort
This open-source Intrusion Prevention System (IPS) defines malicious movements and then generates alerts for users based on any abnormal or suspicious activity. Snort is highly efficient for network traffic debugging and full-blown threat prevention. The tool can be downloaded and configured for both personal use and businesses.
2. Suricata
The next open-source tool is Suricata, which is owned and supported by the Open Information Security Foundation (OISF) - a non-profit that is committed to keeping Suricata open-sourced forever. Suricata can log HTTP requests, log and store TLS certificates, extract files from flows, and store them on disk. Its full pcap capture support also allows easy analysis - making it a powerful engine for a threat-hunting tool.
3. Zeek
Zeek - formally known as Bro - is a threat-hunting solution that monitors and interprets what it sees to create compact, high-fidelity transaction logs, file content, and fully customized output. This output is also suitable for manual review on disk or in a more analyst-friendly tool like a security and information event management (SIEM) system.
Without licensing fees, some enterprises seek out threat-hunting tools like Snort, Suricata, and Zeek, which are rules-based intrusion detection systems (IDS) that focus on network analysis but can also be resource-intensive.
4. Cuckoo Sandbox
This free, open-source tool is perfect for analyzing malware and is an ideal threat-hunting solution. Cuckoo Sandbox can easily monitor different files and allows users to customize the analysis and reports created. Being compatible with Windows, Linux, macOS, and Android makes it suitable for any digital environment.
Cuckoo Sandbox is also made up of a Linux Ubuntu host with a nested Windows 7 system on top of it. The tool’s primary package is based on Python and has multiple dependencies – which can make it difficult to install. VirtualBox is used on the Ubuntu host, while Windows 7 acts as a guest system – with a Cuckoo agent to help the 2 devices communicate.
5. APT-Hunter
The APT-Hunter is a free, open-source tool designed to find abnormal patterns and track APT movements for Windows event logs. The tool notes Mitre ATT&CK tactics and techniques for Windows event log event IDs to help with finding the indicators of an attack.
Learning from previous experiences, the tool can detect an attack faster before containing it. APT-Hunter acts as a filter in your network and speeds up Windows log analysis.
While these open-source threat-hunting services are effective in their ways, commercial security tools can provide guaranteed services and solutions that are essential for bigger organizations. These professional vendors also provide timely and reliable services and updates to keep your network completely secure.
Other Threat Hunting Tools and Platforms
In addition to the previously mentioned top 5 tools, there are several other noteworthy open-source and free options available for threat hunting:
- TheHive: A scalable open-source Security Incident Response Platform, it supports threat hunting through various integrations and offers automated incident response capabilities.
- Moloch: An open-source packet analytics platform, Moloch enables threat hunting through large-scale IPv4 packet capturing, indexing, and real-time network traffic analysis for packet forensics.
- YARA: Specifically designed for malware researchers, YARA helps identify and classify malware samples. It offers cross-platform support (Windows, Linux, macOS) and allows the creation of malware descriptions based on string patterns and boolean expressions.
- Velociraptor: An advanced open-source endpoint monitoring, digital forensics, and cyber response platform, Velociraptor is a versatile tool for threat hunting.
- MISP (Malware Information Sharing Platform): This open-source threat intelligence platform facilitates the sharing of structured information about cybersecurity threats and incidents. It is widely used by SOC analysts, security professionals, and malware reverse engineers for efficient collaboration.
Best Practices for Utilizing the Threat Hunting Tools
To perform these threat hunting tools to the best of their capability, there are several key and best practices to follow:
- Clearly define objectives and establish a dedicated team trained in threat hunting techniques to effectively leverage the tools and understand organizational threats.
- Integrate threat hunting into your cybersecurity strategy by establishing a process that includes data collection, analysis, and response.
- Select tools that align with your organization's needs, considering factors like ease of use, scalability, and integration.
- Stay informed about the latest threats, tools, and techniques. Regularly update your process and tools for effectiveness.
- Maintain transparency by understanding your organization's architecture, communication flows, user behavior, and access to system data.
Sangfor Cyber Command - A Threat-Hunting Cybersecurity That Works for You
Cybersecurity should not take on a “one and done” approach. It needs to be configured carefully and correctly by each organization to ensure the best protection possible.
Open-source threat-hunting software can be a great asset if done properly, but your company deserves a detailed threat-hunting strategy that works for your unique needs and covers all your cybersecurity bases.
That’s where Sangfor comes into the picture. We understand that the best threat-hunting tools are integrated and offer elastic cybersecurity. That’s why the Sangfor Cyber Command platform is the perfect threat-hunting solution. Going well beyond any open-source tools available on the market, the Cyber Command solution ensures that organizations gain full visibility into their network and its threats. With advanced network detection and response capabilities, it monitors internal network traffic, correlates security events using AI and behavior analysis, and identifies hidden threats within the network. By integrating network and endpoint security solutions, Cyber Command enables automated and simplified threat response.
To further deepen your understanding of Sangfor Cyber Command, you might find this video helpful:
Sangfor Cyber Command Success Stories
- J&T Express is a logistics company with the largest shipping volume in Indonesia. Using Cyber Command Security Operations Center, Sangfor conducts regular security assessments for J&T Express. During these assessments, Cyber Command can monitor for brute force attacks, compromised hosts, and high-risk vulnerabilities with Sangfor’s Stealth Threat Analysis (STA).
- The Azienda Socio Sanitaria Territoriale (ASST) Lariana is an established healthcare provider in the Province of Como, Italy. Sangfor Cyber Command gave the healthcare providers 360-degree visibility of the network to ensure cybersecurity.
- Naquadria S.r.l. is a reliable internet service provider and data center based in Piacenza, Italy. Sangfor’s Cyber Command NDR (Network Detection and Response) solution provided Naquadria with a reliable and advanced control and response center for all threats that plagued the exposed systems - including the web and mail servers.
Sangfor is dedicated to providing efficient, effective, and affordable cybersecurity threat-hunting tools and services. For more information on Sangfor’s cyber security and cloud computing solutions, contact us for all your threat-hunting inquiries.
Frequently Asked Questions
The top 5 best open source threat hunting tools are Snort, Suricata, Zeek, Cuckoo Sandbox and APT-Hunter as mentioned above. You can visit their websites and download the latest recommended version.
While open-source threat hunting tools are cheap, they are not always easy to work with and are often incorrectly configured and installed. They are also not powerful or comprehensive enough to protect an entire enterprise. Should the worst happen, and you suffer a cyber-attack, it’s important to consider how your customers will react to your cyber security strategies — will they congratulate you on your frugal approach to cyber security practices – or seek out a company that invests in protecting their data?
Open-source threat hunting platforms do hold a higher level of accessibility to most people who think that deploying professional threat hunting tools might be too costly or include too much red tape. There’s a growing understanding that freely available and easily modified open-source threat hunting gives you the comfort of cybersecurity without the hassle of admin.





